Key Takeaways:
Network penetration testing is about proof, not theory. It demonstrates real exploitability and maps the Path to Compromise, showing exactly how attackers could reach your sensitive assets – not just listing vulnerabilities.
Manual testing delivers authenticity and depth. True network penetration testing relies on skilled human experts who simulate real attacker behavior, uncovering weaknesses and attack chains automated scanners can’t.
Testing validates defenses and compliance. Routine, high-quality penetration tests confirm that your firewalls, segmentation, and security controls actually work under real attack conditions while satisfying frameworks like PCI DSS, SOC 2, and HIPAA.
Proactive testing prevents costly breaches. With the average breach now costing nearly $5 million, regular, comprehensive penetration testing delivers an unmatched ROI and builds customer trust by proving your security readiness.
Network penetration testing is a controlled, authorized attack against your organization’s network infrastructure designed to identify exploitable weaknesses before malicious actors do. It goes far beyond automated scanning, using the same techniques, tactics, and procedures (TTPs) that real attackers employ to breach networks, escalate privileges, and exfiltrate sensitive data.
What is Network Penetration Testing?
Network penetration testing evaluates the security of your organization’s network infrastructure by simulating real-world attacks against firewalls, routers, switches, servers, endpoints, and the connections between them. Skilled security professionals attempt to manually breach your defenses using the same methods employed by threat actors, including reconnaissance, vulnerability exploitation, lateral movement, and privilege escalation.
The goal is not simply to identify vulnerabilities, but to demonstrate actual exploitability and map the Path to Compromise: the chain of weaknesses an attacker would use to move from initial access to your most sensitive assets. This provides contextualized threat intelligence that enables you to build defenses informed by real attack scenarios rather than theoretical risk scores.
External network testing targets internet-facing systems, evaluating how an outside attacker could breach your perimeter. Internal network testing examines security from the perspective of a malicious insider or compromised device already inside your network, testing how far an attacker could move once they gain initial access.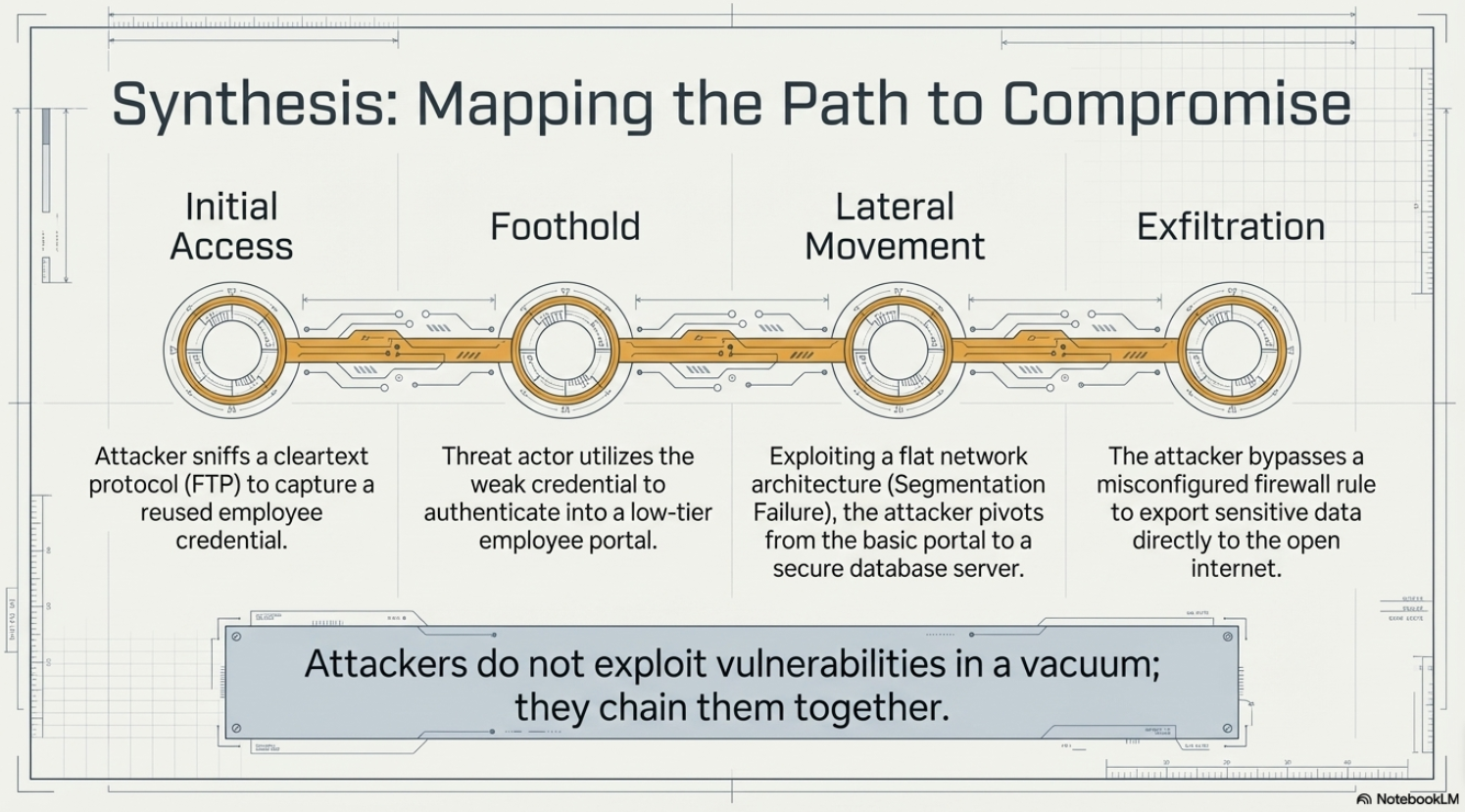
Why Network Penetration Testing is Important
Your network (includes cloud environments) is the backbone of your organization. Every application, every database, every communication flows through it. When attackers breach your network, they gain access to everything connected to it.
The 2024 average breach cost reached $4.88 million. A thorough network penetration test costs a fraction of that investment. If a $40,000.00 test prevents even a single breach, the return exceeds 12,000%. Beyond the financial calculus, network penetration testing reveals whether your security investments actually work. Your firewall rules, network segmentation, intrusion detection systems, and endpoint protections are only effective if they stop real attacks. Testing provides evidence, not assumptions.
Network vs Wireless vs Cloud Penetration Testing
While all three fall under the broader category of penetration testing services, each targets different attack surfaces with distinct methodologies.
Network penetration testing focuses on wired infrastructure: routers, switches, firewalls, servers, and the protocols connecting them. It examines how attackers exploit misconfigurations, unpatched systems, weak credentials, and network segmentation failures.
Wireless penetration testing specifically targets Wi-Fi networks, Bluetooth connections, and other radio frequency attack vectors. Testers evaluate encryption strength, authentication mechanisms, rogue access points, and whether wireless networks provide unauthorized paths into internal systems.
Cloud penetration testing assesses configurations, access controls, and data protection within AWS, Azure, GCP, and other cloud environments. It accounts for the Shared Responsibility Model and often includes testing escalation paths from on-premises networks into cloud resources.
Comprehensive security requires all three. For a complete overview, see our guide on types of penetration testing.
When to Perform Network Penetration Testing?
At minimum, organizations should conduct network penetration testing annually. However, several triggers should prompt additional testing:
- After significant infrastructure changes (new systems, network redesigns, cloud migrations)
- Following mergers and acquisitions to identify security gaps across combined environments
- After security incidents to validate remediations and detect hidden attacker footholds
- Before major product launches or during compliance audit cycles
- When onboarding new vendors or partners with network access
Benefits of Network Penetration Testing
Meeting Regulatory Compliance
- PCI DSS mandates annual penetration testing and testing after significant changes.
- HIPAA expects regular security assessments, and auditors increasingly require penetration testing as evidence of reasonable safeguards.
- SOC 2, ISO 27001, and GDPR frameworks all require or expect regular security validation.
Network penetration testing satisfies these requirements while delivering genuine security value beyond checkbox compliance.
Improve Customer Trust
Many organizations now require penetration testing of vendors as a condition of doing business. Demonstrating regular, thorough security testing differentiates you from competitors who rely on superficial assessments. Customers increasingly understand the difference between genuine testing and automated scans dressed up as penetration tests.
Prevent Data Breaches
The primary benefit is straightforward: finding and fixing vulnerabilities before attackers exploit them. Network penetration testing identifies weaknesses that automated scanners miss, demonstrates actual attack paths, and provides the contextualized intelligence needed to prioritize remediation based on real risk rather than theoretical severity scores.
How is Network Penetration Testing Performed?
Network Discovery & Reconnaissance
Testing begins with intelligence gathering about in-scope network assets. This includes identifying live hosts, open ports, running services, and network topology. Advanced reconnaissance may extend to dark web data, exposed credentials, and information about employees who manage network infrastructure. The depth of reconnaissance reflects the capabilities of actual threat actors.
Scanning & Vulnerability Identification
Testers analyze collected intelligence to identify potential weaknesses: outdated software, missing patches, default credentials, misconfigured services, and insecure protocols. Unlike automated vulnerability scanning, this phase involves human analysis to identify logic flaws and attack chains that scanners cannot detect. Understanding the difference is critical; see our explanation of penetration test vs vulnerability testing.
Exploitation and Impact Analysis
Testers exploit discovered vulnerabilities to demonstrate actual impact. Multiple weaknesses are chained together to establish the Path to Compromise, showing how an attacker moves through the network via lateral movement, escalates privileges, and reaches sensitive data. This phase distinguishes genuine penetration testing from automated scanning: exploitation either succeeds or it does not. There are no false positives.
Reporting, Remediation, and Retesting
Comprehensive documentation includes executive summaries, technical details, risk ratings, and prioritized remediation guidance. Quality reports provide contextualized threat intelligence specific to your environment, not generic vulnerability descriptions. Retesting validates that fixes are effective and ensures no new vulnerabilities were introduced during remediation.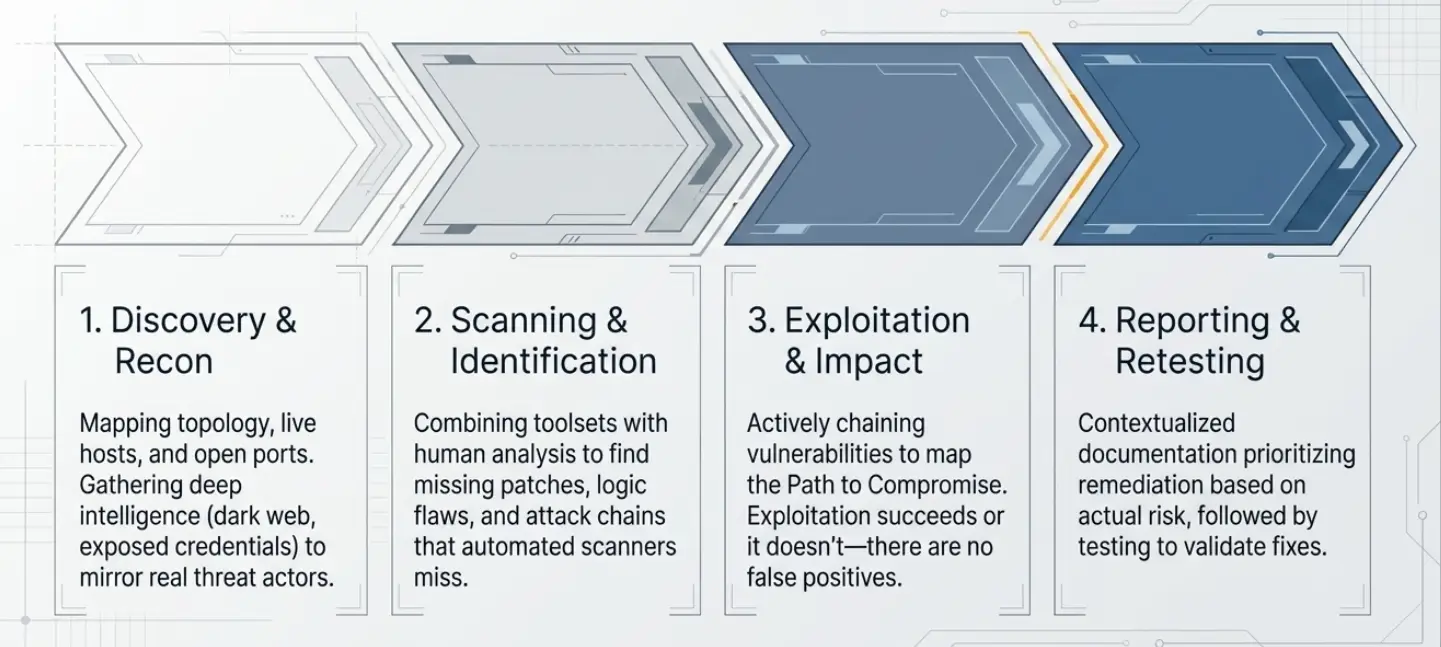
Common Network Vulnerabilities Tested
Insecure Network Protocols
Legacy protocols like Telnet, FTP, and SNMPv1/v2 transmit data in cleartext, allowing attackers to capture credentials and sensitive information. Testing identifies where these protocols remain in use and evaluates whether secure alternatives have been properly implemented.
Weak Credentials
Default passwords, weak password policies, and credential reuse remain among the most common attack vectors. Network penetration testing includes password attacks against services, testing for default credentials on network devices, and evaluating authentication mechanisms across the infrastructure.
Network Segmentation Issues
Proper segmentation limits how far attackers can move once inside your network. Testing evaluates whether sensitive systems are properly isolated, whether VLAN configurations are secure, and whether attackers can pivot from lower-security zones to critical assets. Flat networks with inadequate segmentation allow attackers to move freely once they gain any foothold.
Firewall Misconfiguration
Overly permissive firewall rules, legacy exceptions that should have been removed, and inconsistent policies across firewall clusters create gaps that attackers exploit. Testing evaluates whether your firewall configurations match your security policies and whether rules effectively prevent unauthorized access.
Manual vs Automated Network Penetration Testing
This distinction determines whether you receive genuine security insight or expensive checkbox compliance.
Automated network testing runs vulnerability scanners and/or uses AI, compares results against known issues, and generates reports of known weaknesses. It is fast, cheap, and identifies common issues. It cannot think creatively, chain vulnerabilities in novel ways, or discover zero-day weaknesses.
Manual network penetration testing puts human expertise at the center. Skilled testers analyze your specific environment, identify attack paths unique to your architecture, and exploit weaknesses in ways that reflect actual attacker behavior. They discover business logic flaws, test trust relationships between systems, and demonstrate impacts that scanners cannot anticipate.
Beware of vendors who promise manual testing but deliver automated scans with manual analysis. Genuine manual testing means human experts drive the entire process. For deeper insight into this critical distinction, read our penetration testing guide.
The Future of Network Security
 Network perimeters are dissolving. Remote work, cloud adoption, and IoT proliferation mean organizations no longer have clearly defined boundaries to defend. Zero trust architectures are replacing perimeter-based security models, requiring authentication and authorization for every connection regardless of network location.
Network perimeters are dissolving. Remote work, cloud adoption, and IoT proliferation mean organizations no longer have clearly defined boundaries to defend. Zero trust architectures are replacing perimeter-based security models, requiring authentication and authorization for every connection regardless of network location.
Attack surfaces are expanding faster than security teams can monitor. Every new VPN connection, cloud service, and endpoint security tool adds complexity and new potential vulnerability. Attackers exploit the gaps between and within the systems, targeting misconfigurations in the integrations that connect your infrastructure.
AI and vulnerability scanning will automate baseline reconnaissance and vulnerability identification, but human expertise remains essential for discovering novel attack paths, testing business logic, and emulating sophisticated adversaries. The organizations that thrive will combine automation for efficiency with human creativity for depth. Those that rely entirely on automated tools will continue to be surprised when attackers think beyond the scripts.
Getting Started with Network Penetration Testing
Selecting a qualified vendor is the most important decision. Many providers advertise expert services but deliver repackaged vulnerability scans. Ask about their methodology, their reliance on automation, and whether they can demonstrate research-driven capabilities. Request sample reports and evaluate whether findings reflect genuine manual analysis or reformatted scanner output.
Netragard has delivered genuine, human-driven network penetration testing since 2006. Our Real Time Dynamic Testing methodology uncovers both known and novel vulnerabilities that automated tools miss. Request a Quote to discuss how we can help secure your network infrastructure.
Network Penetration Testing Checklist
- Define scope: internal networks, external perimeter, or both
- Identify critical assets and data that require protection
- Document network architecture and provide topology diagrams
- Establish rules of engagement and communication protocols
- Coordinate timing to minimize operational impact
- Ensure incident response teams are aware testing will occur
- Plan remediation resources before testing begins
FAQ
What are the three types of network service vulnerabilities?
Network service vulnerabilities generally fall into three categories: configuration vulnerabilities (misconfigurations, default settings, excessive permissions), software vulnerabilities (unpatched systems, outdated firmware, known CVEs), and architectural vulnerabilities (poor segmentation, insecure protocols, inadequate access controls). Effective network penetration testing addresses all three.
What commonly exposes a network to vulnerabilities?
The most common exposures include unpatched systems, weak or default credentials, misconfigured firewalls and access controls, legacy protocols transmitting data in cleartext, inadequate network segmentation, shadow IT (unauthorized devices and services), and overly permissive user privileges. Many breaches exploit combinations of these weaknesses rather than single critical vulnerabilities.
Is network penetration testing required for cyber insurance purposes?
Increasingly, yes. Cyber insurance carriers are tightening underwriting requirements, and many now require evidence of regular penetration testing before issuing or renewing policies. Even when not explicitly required, demonstrated security testing can result in more favorable premiums and coverage terms. Testing documentation provides evidence that your organization takes security seriously.
What is Lateral Movement and why is it tested?
Lateral movement refers to techniques attackers use to move through a network after gaining initial access. Once inside, attackers pivot from compromised systems to other hosts, escalate privileges, and work toward high-value targets like domain controllers or database servers. Testing lateral movement reveals whether your internal defenses can detect and contain attackers who breach the perimeter.
Can a pentest help me find Shadow IT?
Yes. Network penetration testing often discovers unauthorized devices, services, and applications that IT and security teams do not know exist. Shadow IT creates unmonitored attack surface and frequently lacks the security controls applied to sanctioned systems. Discovery is often the first step toward bringing these assets under proper management or decommissioning them entirely.
Does network pentesting cover Wi-Fi and wireless entry points?
Standard network penetration testing focuses on wired infrastructure. Wireless penetration testing is typically a separate engagement that specifically targets Wi-Fi networks, Bluetooth, and other radio frequency vectors. However, comprehensive assessments often include both to evaluate whether wireless networks provide unauthorized paths into wired infrastructure. Discuss scope with your vendor to ensure complete coverage.