Key Takeaways:
Automated testing is fast and useful for baseline hygiene, but it only finds known vulnerabilities often months behind real-world threats due to the detection gap.
Manual penetration testing mirrors real attackers by discovering novel vulnerabilities, exploiting business logic flaws, and chaining issues into real Paths to Compromise.
The biggest value of manual testing is contextualized threat intelligence which shows what actually matters in your environment, not just what exists.
AI-driven “penetration testing” doesn’t change the fundamentals; it still relies on pre-existing tools and data, so it cannot think, adapt, or create new attack paths.
The strongest security programs use a hybrid approach: automation for continuous coverage and scale, and manual testing for depth, realism, and true risk validation.
Automated tools find known vulnerabilities that are months old at a minimum. Human testers find known and novel vulnerabilities while building contextualized threat intelligence. That distinction is like the difference between wearing a paper seat belt and a real one. The paper seat belt is a compliance checkbox. The real one is a genuine security exercise that will protect you from real-world attackers. Most “penetration tests” sold today are paper seat belts.
What is Manual Penetration Testing?
Manual penetration testing is a human-driven security assessment where skilled testers emulate the techniques, tactics, and procedures (TTPs) of real-world threat actors. Testers adapt in real time, chain vulnerabilities together, exploit business logic flaws, and map complete Paths to Compromise through your environment. Because human testers are not constrained by pre-defined signatures or pre-trained models, they discover both known and novel vulnerabilities that no automated tool can detect. The result is a precise map of how an attacker moves through your environment from initial access to your most sensitive data. This is contextualized threat intelligence.
That intelligence is how you establish effective threat-informed defenses. Organizations that build defenses around generic intelligence are guessing rather than knowing. It is the cybersecurity equivalent of France’s Maginot Line. France built it based on assumptions about the previous war. Germany simply went around them through the Ardennes. Without that specificity, you are fortifying the wrong areas.
Strengths of Manual Penetration Testing
- Discovers novel and zero-day vulnerabilities that cannot be discovered with AI or automated scanning
- Tests business logic flaws that require human reasoning to identify and exploit
- Chains multiple vulnerabilities to demonstrate complete Paths to Compromise
- Adapts tactics in real time based on what the tester discovers during the engagement
- Provides contextualized threat intelligence that informs defensive strategy
- Produces zero false positives, exploitation either succeeds or it does not
- Evaluates the effectiveness of your detection and response capabilities against realistic attack behavior
Weaknesses of Manual Penetration Testing
Manual penetration testing is not without trade-offs. Organizations should understand these limitations when planning their security testing programs. While the insights delivered by skilled testers are invaluable, the approach requires careful consideration of resource allocation, timeline, and budget constraints.
- Requires more time than automated scanning. Thoroughness is not instant, and rushing a manual test undermines the quality that makes it valuable in the first place.
- Higher cost per engagement, though the ROI is substantially higher when measured against breach prevention. A single prevented breach saves an average of $4.88 million per incident.
- Quality depends entirely on the vendor and skill of the testers. Few vendors deliver genuine manual testing, most sell automated scans with a manual verification step that they misrepresent as a penetration test.
- Limited by the engagement window, though skilled testers maximize coverage (effectively compressing time) through intelligent prioritization, customer collaboration, and in-depth reconnaissance.
What is Automated Penetration Testing?
Automated penetration testing uses software to scan systems against databases of known vulnerabilities. These tools, whether traditional vulnerability scanners like Nessus, Qualys, and Rapid7, or the newer “AI penetration testing” platforms, all operate from pre-defined signatures, pre-trained models, and scripted attack workflows. They identify known vulnerabilities at speed, but they cannot think, adapt, or reason about your specific environment. The fundamental architecture of these tools limits them to detecting what has already been researched, cataloged, and added to their detection capabilities.
AI penetration testing is the latest iteration of this same approach. Despite the marketing hype, AI pen testing tools are just an evolution of automated vulnerability scans. The AI does nothing novel in terms what it tests. Instead, it uses tools from platforms like Kali Linux and determines how to run them. Then it processes their results and determines what the next batch of commands should be. The AI is only capable of predicting based on feedback. It can’t comprehend, and it can’t create anything truly novel.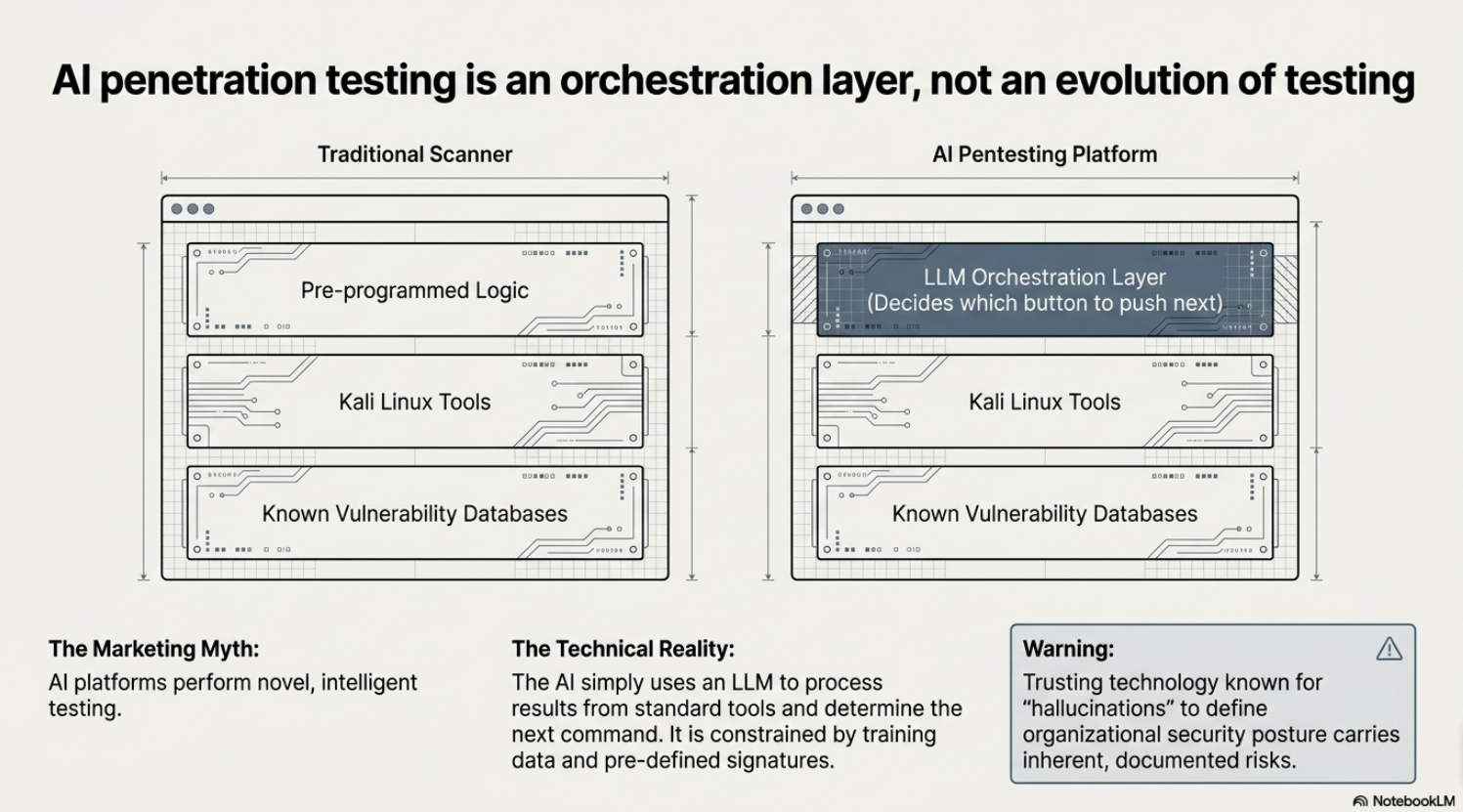
Strengths of Automated Penetration Testing
Despite these limitations, automated tools serve a legitimate purpose in a comprehensive security program. When deployed appropriately, they deliver significant value by identifying known vulnerabilities at scale and enabling continuous monitoring.
- Speed: scans large environments quickly and identifies known vulnerabilities at scale
- Consistency: applies the same checks every time without human variation
- Cost: lower per-engagement cost for baseline vulnerability identification
- Coverage breadth: can scan thousands of hosts, ports, and services in hours
- Maintenance: Useful for continuous monitoring and baseline hygiene between genuine penetration tests
Weaknesses of Automated Penetration Testing
The weaknesses of automated testing are not edge cases. They are fundamental limitations that no amount of scripting or AI can overcome. They stem from the nature of pre-trained and signature-based detection itself.
The core difference between AI penetration testing and traditional vulnerability scanning is orchestration. Traditional scanners use pre-programmed logic with limited decision-making capabilities to determine which tests to run and in what order. AI penetration testing tools replace that pre-programmed logic with a large language model (LLM) and let the LLM decide. The tools they use are almost identical as are the vulnerability databases. The fundamental constraints are the same. The only thing that changed is what decides which button to push next. Considering that AI hallucinations are well documented, trusting that same technology to protect your organization is risky.
Real threat actors are not bound by signature databases or training data. They research, discover, and exploit novel vulnerabilities that no automated system has ever seen. This asymmetry between what automated tools can find and what threat actors can actually do is the core reason why automated testing alone is insufficient for genuine security assurance. The most damaging breaches in history like SolarWinds, Log4Shell, and MOVEit were not caused by known vulnerabilities that a scanner would have caught. They were caused by novel attack chains and creative exploitation that required a human mind to conceive and execute.
Another rarely discussed shortfall is the detection gap. This is the delta between when a vulnerability is discovered and when it becomes detectable by tools. A vulnerability must be discovered, reported to the vendor and disclosed to a CVE authority. Then tool vendors pick it up, analyze the vulnerability, and develop methods for detection. Next the tools need to be tested (quality assurance) and released to customers. Customers then need to update their instances of the tool and run a scan. This entire process can take as little as a few months to as long as a few years.
The gap doesn’t stop there; it often continues until a breach occurs. Unlike human experts, automated tools don’t know how to work around custom configurations, existing security technologies, or communication errors. They lack comprehension. This means these tools will always have a higher rate of false negatives (missed detections) than humans. It also means you’re leaving real windows of opportunity for threat actors to exploit later.
Beyond the detection gap, automated tools have additional fundamental limitations:
- Cannot identify business logic flaws. Human comprehension is required to understand how an application works and to determine whether its specific implementation creates exploitable conditions. No automated tool can reason about business intent.
- Cannot chain vulnerabilities in novel ways. Some vendors claim their tools chain vulnerabilities, but that chaining follows pre-scripted logic, not creative reasoning. The tool chains what it has been programmed to chain. A human attacker chains what actually works in your environment, including paths no one anticipated.
- Cannot adapt tactics during an engagement. Automated tools follow the same scripted workflow regardless of what they encounter. A human tester pivots based on what they discover. A real attacker does the same.
- Cannot deliver contextualized threat intelligence. Automated tools report that a vulnerability exists, but they cannot tell you which findings matter in the context of your specific architecture, and which are noise. Without comprehension, you are left with a list of vulnerabilities and no understanding of what they truly mean for your organization.
When to Use Manual vs Automated Penetration Testing
The question is not which approach is better in isolation. The question is which approach is appropriate for what you are trying to accomplish. If your goal is baseline vulnerability hygiene, automated scanning delivers that efficiently. If your goal is to understand whether your organization can withstand a real attack, only manual penetration testing provides that answer.
Manual Penetration Testing
- When you need to understand whether your organization can withstand a real attack to validate if your security controls, monitoring, and detection actually work against realistic threat actor behavior
- For critical applications handling sensitive data (financial systems, healthcare records, PII)
- When compliance frameworks require genuine penetration testing (PCI DSS, SOC 2, HIPAA, DORA)
- After significant architectural changes, mergers, acquisitions, or new deployments
- When you need defensible evidence of security posture for regulators, auditors, or board reporting
Automated Testing
- For baseline vulnerability hygiene and continuous monitoring across large environments – catching configuration drift, missing patches, and known vulnerabilities between manual tests
- As a preliminary scan before manual testing to eliminate known low-hanging fruit and accelerate the human tester’s workflow
- When budget constraints make manual testing impractical for every system, though critical systems should always receive manual testing regardless of budget
Manual vs Automated Testing
The following table summarizes the key differences between manual and automated penetration testing approaches:
| Capability | Manual Testing | Automated/AI Testing |
|---|---|---|
| Discovers novel/zero-day vulnerabilities | Yes | No |
| Tests business logic flaws | Yes | No |
| Maps complete Paths to Compromise | Yes | No |
| Adapts in real time | Yes | No |
| Provides contextualized threat intelligence | Yes | No |
| Speed across large environments | Slower | Fast |
| Cost per engagement | Higher | Lower |
| False positive rate | Zero | High |
| Detection of newly disclosed vulnerabilities | Immediate | Weeks to months |
| Compliance satisfaction | Full | Partial |
| Emulates Realistic Threat | Yes | No |
Using a Hybrid Approach to Penetration Testing
The most effective security programs use both automated scanning and manual penetration testing, but in the right roles. Automated scanning handles breadth. Manual penetration testing handles depth. The mistake organizations make is conflating the two. Automated scanning is not penetration testing. AI penetration testing is not penetration testing. These tools have a legitimate place in a security program as a complement to genuine human-driven testing, not a replacement for it. Any vendor positioning automated or AI testing as equivalent to manual penetration testing is either uninformed about the technical limitations or deliberately misleading buyers who do not know the difference.
How Netragard Can Drive Your Penetration Testing Needs
Netragard has delivered genuine, human-driven penetration testing since 2006. Our Real Time Dynamic Testing™ methodology identifies both known and novel vulnerabilities because our testers operate at realistic levels of threat taking a research-based approach to testing. We do not rely on signature databases or pre-trained models. Every engagement delivers contextualized threat intelligence mapping the Paths to Compromise through your specific environment, giving you the evidence to build effective threat-informed defenses. Our approach is built on the principle that security testing should deliver real value and that comes in the form of protective benefit.
We use automation where it accelerates our work, not where it replaces expertise. Our testers leverage tools the same way real attackers do, as force multipliers for human skill, not substitutes for it. When we identify a vulnerability, we exploit it. When we chain vulnerabilities, we use expertise not pre-defined scripts. We demonstrate the complete Path to Compromise. When we deliver a report, it contains zero false positives because every finding is the product of human expertise.
Learn more about our penetration testing services, read about how to choose a penetration testing company, or understand the right penetration testing frequency for your organization. Ready to experience genuine penetration testing?
FAQ
Should I run an automated pentest before a manual pentest?
An automated scan before a manual penetration test can be useful for eliminating known low-hanging fruit so the human tester can focus on what matters. Business logic flaws, novel attack chains, and Paths to Compromise that no scanner will find. Think of it as clearing the obvious issues off the table. Just do not confuse the scan with the test itself. The automated scan identifies known vulnerabilities. The manual penetration test determines whether your organization can survive a real attack.
How often should I run manual penetration tests?
At minimum, annually, and after any significant change to your environment such as architectural updates, mergers, acquisitions, new deployments, or major application releases. Organizations in regulated industries or those facing sophisticated threat actors should test more frequently. Automated scanning should run continuously between manual tests to maintain baseline hygiene, but it does not replace the need for periodic human-driven testing. For a deeper look at testing cadence, read our guide on penetration testing frequency.
What is the most cost effective penetration test method?
Automated scanning is cheaper per engagement, but cost effectiveness is not measured by the price of the test. It is measured by what the test prevents. A manual penetration test that identifies a novel attack path to your most sensitive data is dramatically more cost effective than an automated scan that misses it entirely. The average cost of a data breach is $4.88 million. The question is not which test costs less. The question is which test actually reduces your risk.
Are advancements in AI making automated pentests better than manual pentests?
No. AI penetration testing adds an orchestration layer to automated scanning, but it does not overcome the fundamental limitations. AI tools are constrained by their training data. They cannot discover novel vulnerabilities, reason about business logic, or adapt creatively during an engagement. They also face the same detection gap as traditional scanners, weeks to months behind real-world threat actor capabilities for newly disclosed vulnerabilities. The packaging has improved. The limitations have not. Genuine manual penetration testing remains the only method that operates at the same level as the threat actors targeting your organization.