Key Takeaways:
Most “penetration tests” on the market are actually automated scans or AI-driven checks, which create a false sense of security instead of emulating real attackers.
Genuine, human-led penetration testing mirrors real threat actor TTPs, chains multiple vulnerabilities into a Path to Compromise, and delivers contextualized threat intelligence that scanners and AI cannot provide.
Real penetration tests offer massive ROI by preventing multimillion‑dollar breaches, validating security investments, and satisfying regulatory expectations while going far beyond checkbox compliance.
Choosing the right vendor means prioritizing human-driven testing, workload-based scoping, research-backed capabilities, zero false positives, meaningful reports, and included retesting rather than low-cost, automation-heavy offerings.
Penetration testing (aka pen testing) is a controlled, emulated, and authorized cyberattack against your own systems. The objective is to determine how effective your defenses are at protecting your data from real-world attack scenarios.
Frustratingly, the majority of “penetration tests” sold today are not genuine penetration tests. They are automated vulnerability scans or AI penetration tests being misrepresented as genuine penetration tests. These checkbox exercises identify known vulnerabilities but fail to replicate how skilled human attackers actually operate. The difference between a real penetration test and a dressed-up automated scan is often the difference between real security and a false sense of security.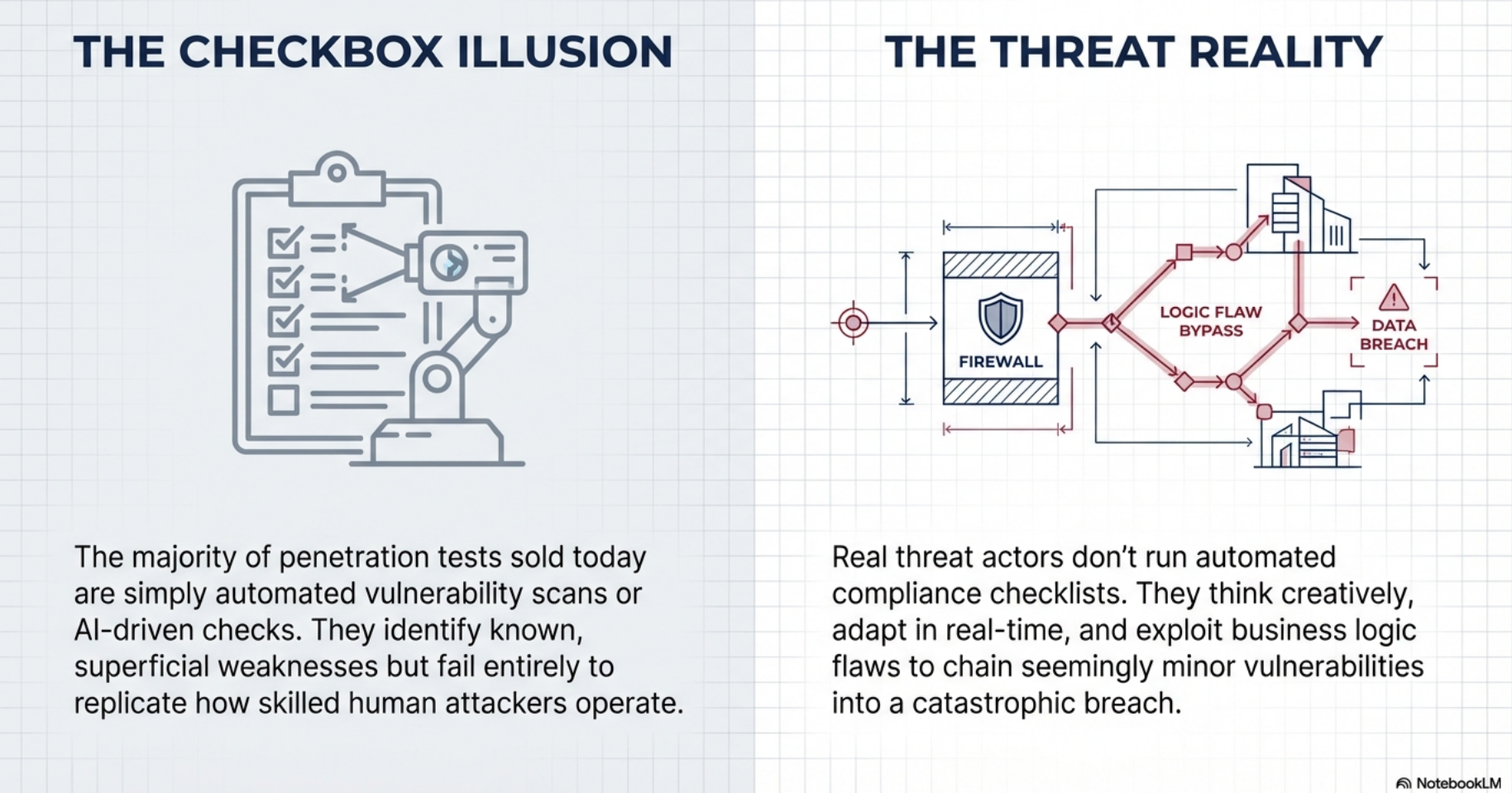
What is Penetration Testing and How Does it Work?
A genuine penetration test emulates the techniques, tactics, and procedures (TTPs) used by threat actors targeting your organization. Skilled experts conduct real-world attacks against your systems, employees, applications, and organization to identify exploitable vulnerabilities and demonstrate actual paths to compromise. The deliverable is a report containing details about all discovered weaknesses and the contextualized threat intelligence required to establish effective threat-informed defenses.
Compliance or checkbox penetration testing is different. It provides bare minimum coverage to satisfy third-party requirements, focusing on known vulnerabilities while missing novel findings. It relies heavily on automation and does not emulate the TTPs of real-world threat actors. The resulting deliverable identifies superficial weaknesses and lacks contextualized threat intelligence.
Genuine penetration testing:
- Emulates how real attackers think, adapt, and exploit systems
- Discovers both known and novel (zero-day) vulnerabilities
- Tests business logic flaws that automated tools cannot understand
- Demonstrates actual exploitability, not theoretical risk
- Maps the Path to Compromise, the chain of vulnerabilities attackers use to reach sensitive data
- Provides actionable intelligence for building threat-informed defenses
Why is Penetration Testing Important?
Genuine penetration testing delivers massive ROI. In 2024, the average breach cost $4.88 million while a genuine penetration test costs around $40,000. If that test prevents even a single breach, the ROI exceeds 12,000%.
Beyond the numbers, genuine penetration testing delivers:
- Reduced risk. Contextualized threat intelligence reveals how attackers would exploit your specific weaknesses.
- Limited breach impact. Threat-informed defenses enable early detection, containing lateral movement and minimizing data loss.
- Competitive differentiation. Many organizations require penetration testing of vendors as a condition of doing business.
- Validation of security investments. Testing reveals whether your SIEM, EDR, and firewalls actually work against real-world threats.
- Executive visibility. Concrete evidence of security posture for leadership, not just “we passed an audit.”
- PCI DSS, HIPAA, SOC 2, ISO 27001, and GDPR require or expect regular security testing.
Human-Led Penetration Testing vs. Automated Testing
This is the most critical distinction in the industry. While every vendor promises manual penetration testing, very few deliver. Beware of automated vulnerability scans followed by manual exploitation attempts masquerading as penetration tests. Those are vetted vulnerability scans, not genuine tests. Human experts must drive the entire process, uncovering vulnerabilities that scanners and AI cannot detect.
| Aspect | Human-Led Testing |
Automated/AI Testing |
|---|---|---|
| Vulnerability Coverage | Known and novel (zero-day) | Known only |
| Business Logic | Detected through reasoning | Cannot detect |
| Attack Paths | Maps complete Path to Compromise | Superficial |
| Adaptability | Adapts in real time | Fixed workflows |
The Penetration Testing Process
The exact process varies per customer requirements and threat level, but genuine penetration testing follows these phases:
Scoping & Planning
Scope determines cost, and cost is based on measured workload, not IP addresses or page counts. Workload is derived from in-depth discussions and hands-on discovery. Vendors who price based on count will deliver compliance penetration tests.
Reconnaissance & Intelligence Gathering
Gathering intelligence about in-scope targets before launching attacks. This can be basic (live hosts and open ports) or advanced (dark web data and personal details about targeted employees).
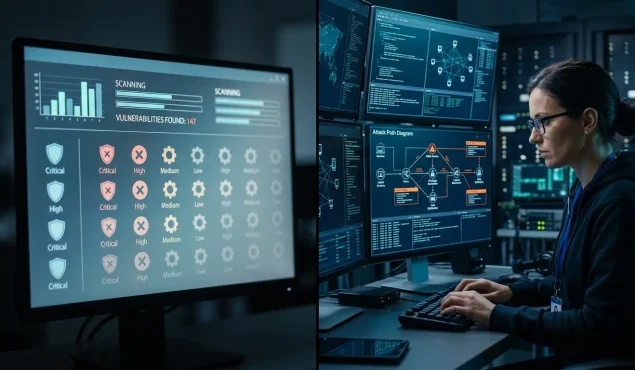
Vulnerability Discovery & Analysis
Reviewing collected intelligence to identify vulnerabilities, from outdated systems and missing patches to human behaviors that create social engineering opportunities.
Exploitation and Attack Simulation
Exploiting discovered vulnerabilities to demonstrate impact. Multiple weaknesses are chained to establish the Path to Compromise, showing how an attacker moves from initial access to sensitive data through lateral movement, privilege escalation, and emulated data exfiltration.
Reporting & Documentation
Comprehensive documentation including executive summaries, technical details, risk ratings, and prioritized remediation guidance. Quality reports provide contextualized threat intelligence, not just a list of CVEs (Common Vulnerabilities and Exposures).
Remediation Support & Validation
Free retesting to verify fixes and ensure no new vulnerabilities were introduced. Ongoing support for knowledge transfer and maximum customer value.
How Penetration Testing Simulates and Differs from Real-World Attacks
Genuine penetration testing replicates attacker behavior as closely as possible within authorized boundaries. Testers use the same or better reconnaissance techniques, exploitation methods, and lateral movement strategies as real threat actors. The difference is intent: penetration testers document vulnerabilities without causing damage; real attackers exploit them for profit, disruption, or espionage.
When Should a Company Perform Penetration Testing?
 The short answer: it depends. Ideally, penetration testing should occur after significant changes to infrastructure, applications, or corporate structure. It should also be conducted during mergers and acquisitions to identify security gaps and normalize security across combined entities.
The short answer: it depends. Ideally, penetration testing should occur after significant changes to infrastructure, applications, or corporate structure. It should also be conducted during mergers and acquisitions to identify security gaps and normalize security across combined entities.
At minimum, penetration testing should be performed annually across your entire organization, including external and internal infrastructure, web applications, incident detection and response capabilities, and employees via social engineering. Testing is also recommended after security incidents to validate remediations and identify hidden footholds attackers may have left behind.
Common Misconceptions About Penetration Testing
The terms penetration testing, vulnerability scanning, ethical hacking, AI penetration testing, and red teaming are often used interchangeably, but they represent fundamentally different approaches with different capabilities and outcomes.
| Capability | Genuine Pen Testing | Vulnerability Scanning | AI Pen Testing | Ethical Hacking |
|---|---|---|---|---|
| Human-driven analysis | ✓ | ✗ | ✗ | ✓ |
| Discovers novel (zero-day) vulnerabilities | ✓ | ✗ | ✗ | ✓ |
| Tests business logic flaws | ✓ | ✗ | ✗ | ✓ |
| Maps complete Path to Compromise | ✓ | ✗ | Partial | Varies |
| Chains multiple vulnerabilities | ✓ | ✗ | Limited | ✓ |
| Adapts tactics in real time | ✓ | ✗ | ✓ | ✓ |
| Emulates real threat actor TTPs | ✓ | ✗ | Limited | Varies |
| Provides contextualized threat intelligence | ✓ | ✗ | ✗ | Varies |
| Structured testing methodology | ✓ | ✓ | ✓ | Varies |
| Satisfies compliance requirements | ✓ | Partial | Partial | Varies |
Penetration Testing vs. Vulnerability Scanning
A vulnerability scan identifies known weaknesses by comparing systems against signature databases. A penetration test proves those weaknesses can be exploited, chains them together, and maps the Path to Compromise. Many vendors blur this distinction, selling scans as “penetration tests” at lower prices. 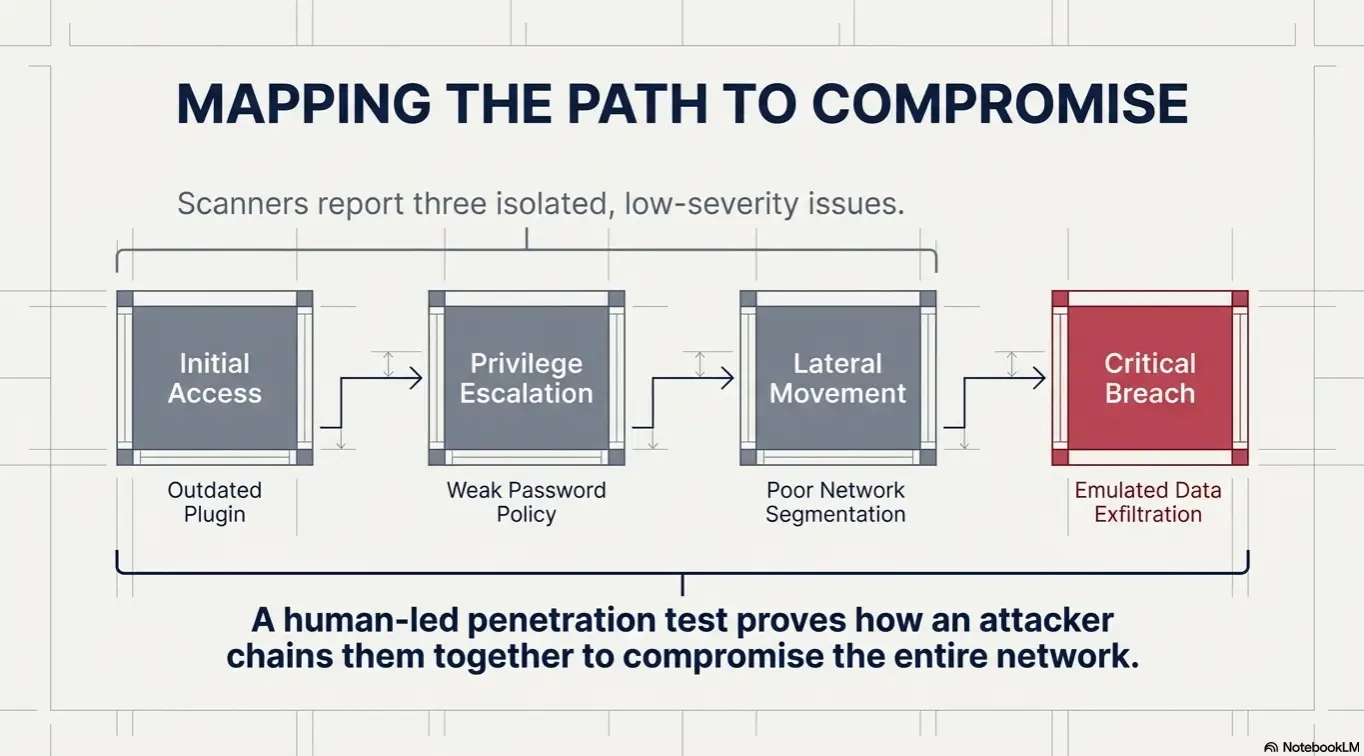
Penetration Testing vs. AI Penetration Testing
AI penetration testing is the latest iteration of a familiar pattern: vendors repackaging automated tools as something they’re not. Just as vulnerability scanners were dressed up and sold as penetration tests, AI penetration testing is now being positioned as a faster, cheaper alternative to human-led testing. The reality is that AI penetration testing is simply the next evolution of automated vulnerability scanning.
AI acts as an orchestrator. It runs known tools, follows scripted workflows, and chains pre-programmed attacks. It cannot think creatively, adapt to context, or exploit business logic flaws. What AI cannot do is what matters most: chain vulnerabilities in ways no automated system can anticipate, discover novel attack methods and zero-day vulnerabilities, and understand the business context that makes certain vulnerabilities catastrophic while others are trivial.
Real threat actors use AI, but not to replace their skillset. They use it to enhance their capabilities: automating reconnaissance, generating phishing content, and scaling attacks. The human attacker remains at the center, making decisions and exploiting opportunities that automation cannot recognize. This is exactly how AI should be used in penetration testing: as a force multiplier for skilled human testers, not as a replacement for them.
Penetration Testing vs. Ethical Hacking
Ethical hacking is a broad term for authorized security testing: reverse engineering hardware, writing exploits, auditing code. Penetration testing is a specific, structured form of ethical hacking focused on emulating threat actors to validate organizational security. All penetration testing is ethical hacking, but not all ethical hacking is penetration testing.
Penetration Testing vs. Red Teaming
Red teaming is mission-oriented with specific objectives: compromise the CEO’s email, exfiltrate customer data. It stays focused, exploiting only what’s needed to satisfy mission objectives. Penetration testing provides broad coverage, identifying as many vulnerabilities as possible. Netragard’s Platinum services with Threat Augmentation Modules bridge this gap.
Types of Penetration Testing
Network Penetration Testing
Evaluates firewalls, routers, switches, servers, and endpoints. External testing targets internet-connected systems; internal testing evaluates security from the perspective of a malicious insider or compromised device. Both map how attackers move laterally to reach sensitive data.
Cloud Penetration Testing
Assesses configurations, access controls, and data protection in AWS, Azure, GCP, and other cloud environments. Testing accounts for the Shared Responsibility Model and can include escalation from on-premises networks into cloud resources.
Wireless Penetration Testing
Tests wireless network security including encryption, authentication, and segmentation. Identifies rogue access points and evaluates whether wireless networks provide unauthorized paths into internal systems.
Who Needs Penetration Testing?
Every organization that relies on technology to operate, stores sensitive data, or would suffer consequences from a breach. Attackers don’t discriminate based on company size. They target opportunity.
Small and Mid-Sized Businesses
SMBs are increasingly targeted as easier targets than large enterprises. A genuine penetration test ($15,000 to $40,000) is a fraction of the $4.88 million average breach cost. For many SMBs, a single breach is existential. Silver or Gold level testing matches risk profile to budget.
Enterprise Organizations
Large enterprises face nation-state actors, organized cybercrime, and APTs with significant resources and patience. Complex environments with thousands of endpoints, legacy systems, and cloud integrations create attack surfaces where vulnerabilities hide in the gaps. Platinum-level testing with maximum depth and threat intensity identifies vulnerabilities before advanced attackers do.
Healthcare, Finance, and Regulated Industries
Organizations subject to HIPAA, PCI DSS, SOC 2, GDPR, and other data regulations require penetration testing that satisfies compliance while providing genuine security value. Checkbox testing may satisfy auditors who don’t know the difference, but it won’t prevent breaches.
How to Choose a Penetration Testing Vendor
Selecting the right vendor is complex. Many vendors advertise best-in-class services, use the same terminology, and make the same promises. A vendor’s true expertise often remains unknown until after services have been rendered. The baseline for penetration testing quality is established by the tactics and capabilities of real-world threat actors. If a vendor’s expertise falls short of real-world threats, their services will have significant gaps in coverage.
Key questions to ask:
- What percentage of testing is done with automated scanners? The greater the dependence on automation, the lower the quality. Manual penetration tests should not merely be manual analysis of vulnerability scan results.
- How do you price engagements? Count-based pricing (per IP address, per page) indicates dependence on automation. Workload-based pricing, determined through diagnostic discovery, indicates genuine manual testing.
- Does your company perform vulnerability or zero-day research? Ask for published advisories or research documents. If they cannot produce proof of research, they likely do not have research-driven capabilities.
- How many false positives do your reports contain? Penetration test deliverables should never contain even a single false positive. Exploitation either succeeds or it doesn’t.
- Can you provide an example report? Look for depth of findings (business logic errors, multi-step exploitation), detailed reproduction steps, and customized analysis. Reports that are merely reformatted scanner output indicate checkbox testing.
- Are retests included and do they expire? Quality vendors retest to verify remediations. Retests should be conducted within 60 to 90 days while the assessment is still relevant.
The Future of Penetration Testing
As attack surfaces expand with cloud adoption, IoT, and remote work, penetration testing becomes more critical, not less. AI will automate baseline tasks, but human expertise remains essential for discovering novel vulnerabilities, testing business logic, and emulating sophisticated attackers. Organizations that understand the difference between genuine testing and checkbox exercises will prevent breaches. Those that don’t will continue to be surprised.
Getting Started with Penetration Testing
Netragard has delivered genuine, human-driven penetration testing since 2006. Our Real Time Dynamic Testing™ methodology, derived from vulnerability research and exploit development practices, uncovers both known and novel vulnerabilities that automated tools miss. Whether you need Silver-level testing for compliance, Gold-level depth for critical applications, or Platinum-level threat intensity that exceeds real-world attacks, we deliver evidence, not guesses, about whether your defenses actually work.
Ready to experience genuine penetration testing?
FAQ
Does penetration testing disrupt live production systems?
Professional penetration testing is designed to identify vulnerabilities without causing lasting disruption. Skilled testers coordinate with your team to minimize impact, avoid sensitive operational windows, and use controlled techniques. Any actions that could cause significant disruption are discussed and approved in advance during scoping.
Does penetration testing access or view sensitive customer or patient data?
Penetration testers aim to demonstrate that sensitive data could be accessed, not to actually collect or view it. Engagements include strict rules of engagement protecting sensitive data. Testers emulate data exfiltration using mock data or demonstrate access paths without viewing actual records.
Is penetration testing required for compliance (HIPAA, PCI DSS, SOC 2)?
PCI DSS explicitly requires annual penetration testing and testing after significant changes. HIPAA requires regular security assessments, and auditors increasingly expect penetration testing as part of demonstrating “reasonable and appropriate” safeguards. SOC 2 and ISO 27001 require regular testing of security controls. Genuine penetration testing, not just vulnerability scanning, is increasingly expected across regulatory frameworks.
How much does penetration testing cost?
Genuine penetration testing for SMBs typically ranges from $15,000 to $40,000. Enterprise engagements with complex environments may cost more. Be wary of “penetration tests” for a few thousand dollars. These are almost certainly automated vulnerability scans. The investment pales in comparison to the $4.88 million average breach cost.