The Play ransomware group, also referred to as Playcrypt, emerged in June 2022 and has since remained active in the threat landscape. Although similarities between Play and the Hive ransomware group have led some analysts to speculate about potential overlap in operatorship, there are notable distinctions between the two. Unlike Hive, Play does not operate using a Ransomware as a Service (RaaS) model. Instead, Play develops its own malware and executes attacks independently. Moreover, Play is recognized for employing advanced Techniques, Tactics, and Procedures (TTPs) that contribute to their sophisticated approach. We can leverage those TTPs with Realistic Threat Penetration Testing to help improve ransomware protection
Just recently, On May 12th, 2023 the City of Lowell, Massachusetts reported that they had fallen victim to the Play ransomware group. While the specific details regarding the method of breach into Lowell’s network have not been disclosed, it is reasonable to assume that they used the same or similar TTPs as those used in previous attacks. It should be noted that as with any capable threat actor, Play’s TTPs evolve over time.
As a double extortion group, Play follows a consistent modus operandi: infiltrating their victims’ networks, moving laterally to access sensitive data, exfiltrating the data, and subsequently encrypting the victim’s files. They then issue a ransom demand, accompanied by the threat of publishing the stolen data—a tactic known as double extortion—if their demands are not met. As of May 11th, 2023, Play had already released 5 gigabytes of data stolen from Lowell. According to Play’s website on the darkweb, this data includes “private and personal confidential data, finance, taxes, clients, and employee information.” This release is intended to be a warning shot to demonstrate that Play in fact has the data and is prepared to release if the victim does not participate.
It is common for ransomware victims to ask for assistance only after falling victim to an attack, which is not an effective approach. Organizations need to take a proactive approach to safeguard themselves before they are targeted. One of the most effective methods of defense is to subject your organization to penetration testing that specifically utilizes TTPs that match the capabilities of those employed by the threat actors. This approach, known as Realistic Threat Penetration Testing, offers significant advantages. The following provides a high-level overview of how we might incorporate Play’s known TTPs into a Realistic Threat Penetration Test to facilitate effective ransomware protection.
Initial Access
This is the first step or method used by an attacker to gain entry to a target system or network. It involves finding and exploiting vulnerabilities or weaknesses in the target’s defenses to establish an initial foothold.
Play Ransomware Group
Play reuses stolen credentials (including VPN accounts), social engineering, and/or vulnerability exploitation to gain initial access to a victims’ network. They have also been known to target exposed RDP servers, and to exploit vulnerabilities in Fortinet (CVE-2020-12812 and CVE-2018-13379).
Ransomware Protection from Realistic Threat Penetration Testing
With realistic threat penetration tests we leverage our partnerships with various data aggregators that collect data compromised (including stolen credentials) during third-party breaches. Extracting credentials, among other data, is as easy as performing a standard web search for a domain, email address, or IP address. Then, like Play’s modus operandi, a realistic threat penetration test would attempt to utilize these stolen credentials to gain initial access to the targeted organization’s systems and networks. If that approach does not work then the tactics would change to target and exploit known vulnerabilities like the ones used by Play, or novel vulnerabilities that we discover on the fly. If those options do not work, then testing would change tactics again to leverage advanced social engineering, which rarely fails.
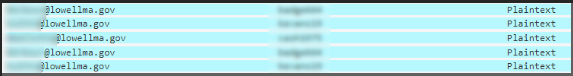
By way of example, we performed a search of records stolen during third party data breaches for the domain lowellma.gov. That search returned 691 records containing passwords which suggest that this may have been the method of access used by Play when they breached the City of Lowell. To be clear, this information is publicly available and bad actors know how to access it.
Lateral Movement
After gaining initial access, the Play ransomware group initiates lateral movement, which is the propagation of a breach across the compromised infrastructure. A realistic threat penetration test would replicate the techniques employed by the Play ransomware group. The following is an example of some of Play’s TTPs and how we might apply them when testing a customer.
Post Breach Network Discovery
Network discovery, or reconnaissance, is the process of gathering information about a target network to discover and later exploit vulnerabilities. This is the most vulnerable point of the attack for threat actors because if the victim has honeypots setup, the activity generated here is likely to be detected.
Play Ransomware Group
Play is recognized for employing innovative tools such as Grixba, a robust network-scanning and information-gathering tool. Grixba utilizes various protocols like WMI, WinRM, Remote Registry, and remote services to conduct scans and gather details about the software installed on devices within a network. It comprehensively checks for the presence of antivirus and security programs, EDR suites, backup tools, remote administration tools, as well as commonly used office applications and DirectX to gain insights into the targeted systems.
Realistic Threat Penetration Testing
Rather than Grixba, Netragard replicates some of these capabilities using Impacket, a powerful and widely used Python library that provides a set of tools and APIs for interacting with network protocols, performing network attacks, and developing custom network applications. We also create custom toolsets or use existing trusted tools when needed.
Credential Access
This involves collecting credentials, or if credentials were used to breach, additional credentials with increased privileges.
Play Ransomware Group
Play has been known to use common tools like Mimikatz, a post-exploitation tool that is primarily used for extracting and manipulating authentication credentials from compromised systems.
Realistic Threat Penetration Testing
The Netragard team also uses Mimikatz to extract credentials from memory, which plays into persistence and privilege escalation.
Privilege Escalation
This is the process of elevating access privileges within a system or network to gain higher levels of control. This can be accomplished by capturing credentials, or by exploiting vulnerabilities, misconfigurations, and weaknesses in security controls.
Play Ransomware Group
Play escalates privileges by also using Mimikatz to extract higher privileged credentials from the memory of systems it compromises. When it gains access to an account with sufficiently high privileges it adds an account to privileged groups, one of which is the Domain Administrators group.
Realistic Threat Penetration Testing
Netragard also uses Mimikatz, as well as other techniques to capture credentials for accounts with elevated privileges. Like Play, we also create accounts in the Domain Administrators group.
Evasion
Evasion refers to the techniques and strategies employed by threat actors to bypass or circumvent security measures, detection mechanisms, and monitoring systems, allowing them to operate undetected and carry out malicious activities.
Play Ransomware Group
Play has been seen using tools like Process Hacker, GMER, IOBit, and Powertool to disable malware monitoring solutions. They also disable Windows Defender protections through the use of PowerShell or command and use additional tools like Cobalt Strike BEACON and Empire.
Realistic Threat Penetration Testing
When needed, Netragard also uses Process Hacker, GMER, IOBit, Powertool and Empire. We use a platform with the same capabilities as Cobalt Strike.
Persistence
Persistence is the ability of an actor to maintain a presence or re-establish itself on a compromised system or network, even after a reboot or other disruptive events. It involves employing techniques and mechanisms to ensure continued access and control, enabling further malicious activities, or facilitating future unauthorized access.
Play Ransomware Group
Play achieves persistence by using the valid accounts it captures during its activities and leveraging the Remote Desktop Protocol (RDP) to access systems at will. If RDP is disabled, play enables it using “netsh”.
Realistic Threat Penetration Testing
Using captured credentials has been Netragard’s primary and favored method for maintaining persistence for some time. One of the main advantages of this method is that it enables us to present ourselves as a trusted user within our customer’s network, which is ideal for evading detection. Other methods of persistence include using RADON, our pseudo-malware, and certain scripts.
Data Exfiltration
This is the act of extracting or stealing a victim’s data.
Play Ransomware Group
Play usually splits a victim’s data into chunks to reduce the size of the files being exfiltrated. They often use WinSCP for transfers and WinRAR to generate compressed archives for more efficient transfer. Play has also been observed setting up a PHP website to receive the exfiltrated files.
Realistic Threat Penetration Testing
Our team at Netragard simulates exfiltration by either creating a specific file on a compromised system or exfiltrating a file or files created by our client (a trophy). At no point will we copy, manipulate, exfiltrate, or deliberately access a customer’s sensitive data (unless expressly requested and authorized).
Impact
The consequences and effects of a cyberattack or security incident, which can include financial losses, operational disruptions, compromised data, reputational damage, and potential legal and regulatory consequences for the affected organization or individuals.
Play Ransomware Group
The impact associated with a data breach from Play includes substantial financial impact, loss of customer confidence, reputational damage, and in some cases could even cause an organization to cease operations.
Realistic Threat Penetration Testing
The return on investment of Realistic Threat Penetration Testing is equal to the cost in damages that would otherwise be realized from a successful data breach. Ransomware prevention is directly attributed to the application of the findings from a realistic threat penetration test but those findings will only be as effective as the penetration test is realistic.
The penetration testing report produced from a realistic threat penetration test offers valuable insights into an organization’s defense capabilities when challenged by a sophisticated real-world threat. By undergoing these services, organizations can proactively assess their security posture, harden weaknesses, and develop effective defenses, significantly reducing the risk of becoming a victim of a data breach. The investment in these services is a small fraction of the potential costs incurred from the aftermath of a single successful data breach.
For more information on realistic threat penetration testing services please contact us here.