Its funny to me that people haven’t commented on the fact that the ability of a worm to spread is proof positive of just how insecure today’s networks are. (Yet, even with this lack of security others are talking about this kick-ass idea of “Cloud Computing”). The fact is that if people managed their networks properly (which includes testing properly with quality security service providers) that worms like Conficker would not be able to spread, or at least not so quickly and on such a wide scale.
As an example, we recently performed a penetration test for one of our customers. The time between project kickoff and successful penetration was less than 15 minutes. That is to say that we were able to hack into our customers network within 15 minutes of starting the project. The way we did it was to create a .pdf based invoice and send it to the customer from a trusted source. This particular invoice wasn’t really an invoice of course, it was a pdf document designed to exploit a vulnerability in their adobe acrobat reader. In this case, when our victim opened the pdf document their computer established a reverse http connection back to us (like Conficker). We then tunneled back in over that connection and had access to our customer’s network. If we were malicious it would have been game over.
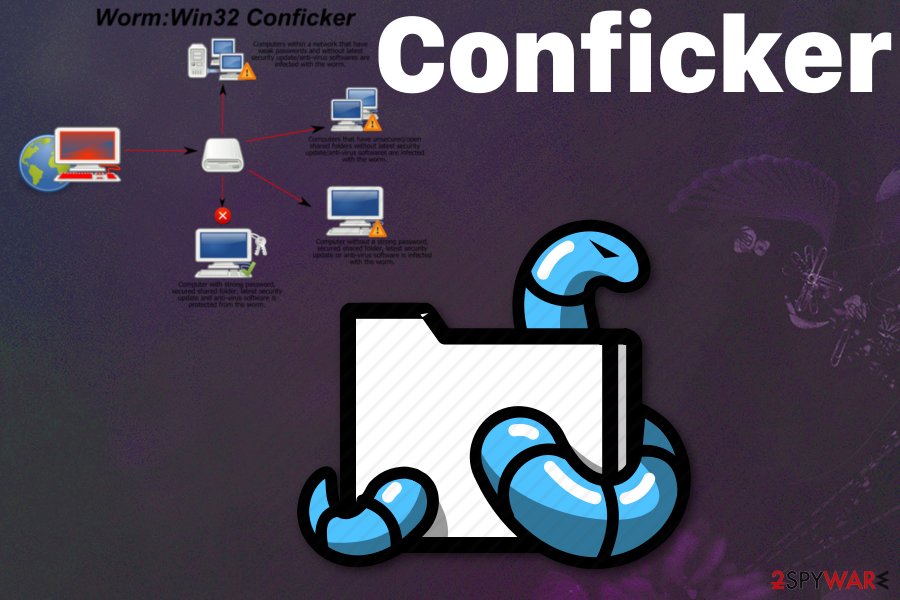
So what does this have to do with malware like Conficker? If you think about it a worm uses the same methodology for penetrating into networks as hackers do. Just like hackers, worms will penetrate a network by embedding themselves in files (like our PDF example above), or by exploiting vulnerabilities in computers systems, or maybe via social engineering. Either way, the technique is the same, and as such the defense should be the same. Why isn’t it?
Most people _try_ to protect their networks with anti-virus scanners and other technology. They implement these scanners on their desktops, servers, gateway’s etc. They also use Intrusion Detection/Prevention Systems, firewalls and other similar solutions in an attempt to prevent infection or penetration. They never stop to question the security of the technology that they install. In 2006 Symantec’s own Antivirus technology was vulnerable to attack. Back then it was possible to send someone a specially crafted email to penetrate into their computer. The fact is that technology is, and will always be fallible unless it is proved to be secure with mathematics.
I’m not saying that technology is useless because it isn’t. I am saying that technology should be augmented with frequent security testing. Those tests should be delivered by a quality security provider capable of creating a threat that is at least as intense as what customers will face in the real world. Once testing is done at that “real” level the resulting deliverable will enable people to build good defenses that are based on solid recommendations.
Continuing with the pdf customer… One of the recommendations that we made to our customer was that they install a proxy to control outbound http and https traffic. We also recommended that they drop all outbound traffic that is not necessary for day-to-day business operations. We made that recommendation because of how easily we penetrated their network with PDF and the reverse http connection.
The customer implemented our recommendations and when we retested their network were unable to get anything to call home. As a result of our work worms like Conficker can not function properly on our customer’s network because they can not call home. Instead, if they do get in they sit on the network isolated and useless until they are eliminated by the anti-virus technology.