Key Takeaways:
- Threat-Led Penetration Testing (TLPT) goes beyond traditional pen tests by emulating real attacker TTPs against live production, testing technology, processes, and people to answer “can we survive a real attack?” rather than just “where are we vulnerable?”.
- Under DORA, TLPT is a mandatory, intelligence-led exercise for significant financial entities, run at least every three years on critical live production systems (including key third parties), with strict requirements for tester qualifications, external threat intelligence, purple teaming, and comprehensive documentation for regulators.
- TLPT’s value comes from contextualized threat intelligence: it tailors scenarios to your industry, geography, infrastructure, and business operations, revealing how real adversaries would chain technical flaws, business logic weaknesses, and human factors in ways that automated or “AI-based” testing cannot replicate.
- Netragard positions its Platinum service as TLPT, combining contextualized threat intel, its Real Time Dynamic Testing™ methodology, and experienced human operators to deliver realistic, regulator-aligned testing and highly actionable outputs that support purple teaming and measurable resilience improvements.
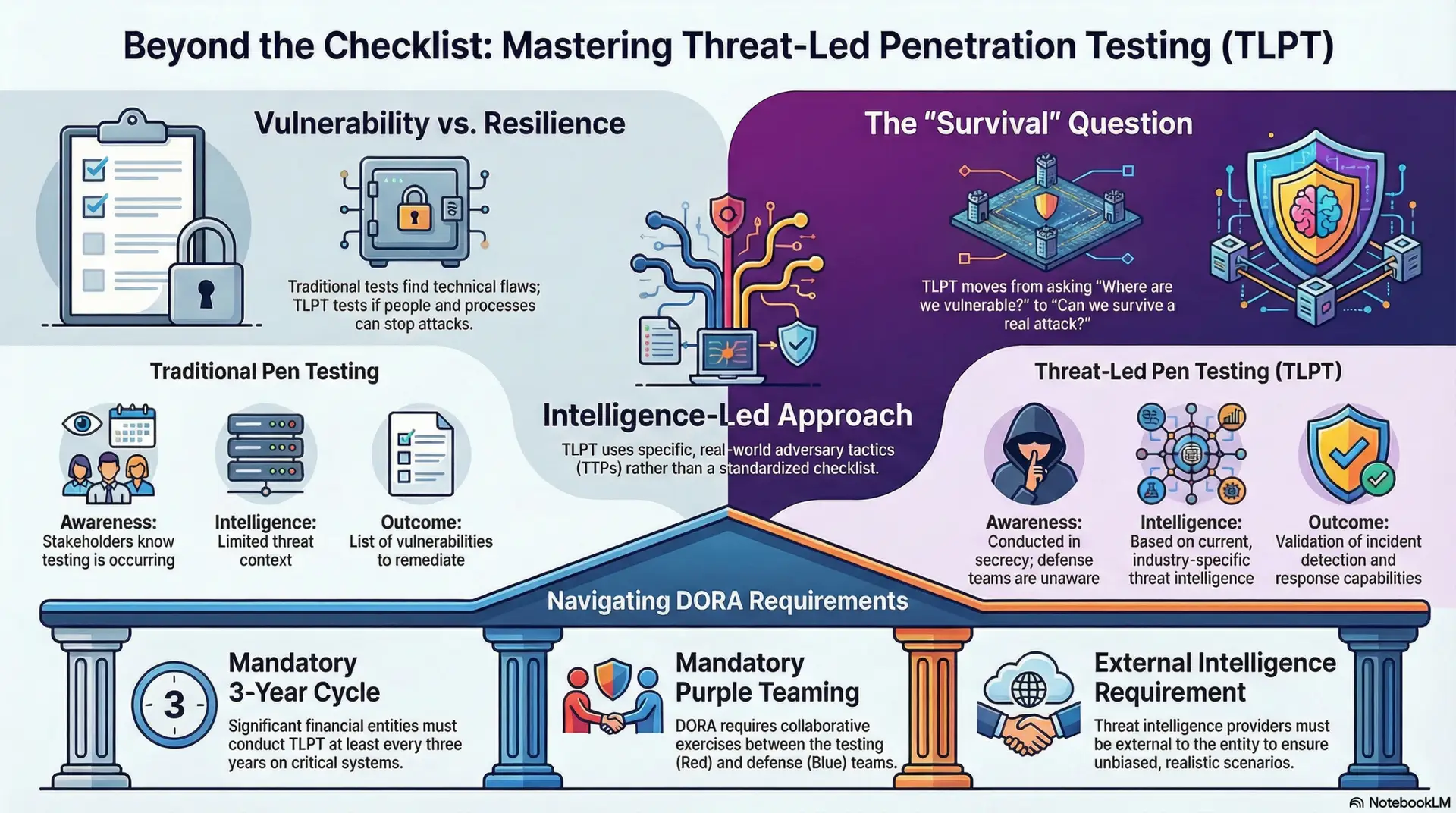
Most penetration tests check whether you’re vulnerable and provide little to no security value. Threat-Led Penetration Testing (TLPT) checks whether you can detect and stop a real attack in progress.
That distinction matters. Traditional penetration testing identifies technical weaknesses in isolated systems. TLPT tests your entire organization, technology, processes, and people, against the tactics real attackers use right now.
For financial institutions operating under the Digital Operational Resilience Act (DORA), TLPT is not optional. It is a regulatory requirement designed to validate operational resilience against genuine cyber threats.
What is Threat-Led Penetration Testing (TLPT)?
Threat-Led Penetration Testing is an intelligence-driven exercise that emulates real-world attack scenarios against an organization’s critical live production systems. Unlike standard penetration testing, which follows a checklist approach to find known vulnerabilities, TLPT safely uses the tactics, techniques, and procedures (TTPs) of actual threat actors who pose a genuine risk to your organization.
DORA defines TLPT as “a framework that mimics the tactics, techniques and procedures of real-life threat actors perceived as posing a genuine cyber threat, which delivers a controlled, bespoke, intelligence-led (red team) test of the financial entity’s critical live production systems.”
The objective is clear: determine whether your defenses can detect, respond to, and contain a sophisticated cyber-attack, not just whether vulnerabilities exist.
It’s important to clarify that despite DORA’s use of the term “red team”, TLPT and Red Teaming are substantially different. Red Teaming engagements are far broader, can span months or more, target physical, human and digital assets, and have clear mission objectives. In terms of Netragard’s services, our Platinum Level service is TLPT while Ruby Red is our Red Teaming offering.
How TLPT Differs from Traditional Penetration Testing
| Aspect | Traditional Penetration Testing | Threat-Led Penetration Testing (TLPT) |
|---|---|---|
| Scope | Specific systems or applications | Entire organization including critical functions |
| Focus | Technical vulnerabilities | Technology, processes, and people |
| Approach | Standardized checklist methodology | Intelligence-driven, customized attack scenarios, research driven methodology |
| Awareness | Stakeholders know testing is occurring | Conducted in secrecy; defense teams unaware |
| Intelligence | Limited threat context | Based on current threat intelligence derived from various aggregators |
| Outcome | List of vulnerabilities to remediate | Validation of incident detection and response capabilities as well as overall resilience |
| Duration | Days to weeks | Weeks to Months |
- Traditional penetration tests answer the question: Where are we vulnerable?
- TLPT answers a different question: Can we survive a real attack?
Example of Threat-Led Penetration Testing (TLPT)
Consider how Netragard approached a threat-led penetration test against a well-known casino. The engagement began with extensive threat intelligence and reconnaissance, we used proprietary tooling to extract employee information from LinkedIn, including names, titles, employment history, and contact details. We leveraged a Google username enumeration vulnerability to validate email addresses and built a targeted list for social engineering.
Based on this intelligence, we crafted attack scenarios replicating real threat actor behavior. We registered a “doppelganger domain”, a lookalike domain designed to impersonate the casino’s legitimate domain (for example, acmecorporatlon.com instead of acmecorporation.com) complete with SSL certificates, SPF records, and DKIM to evade email security controls. We geolocated employees using social media, leaked data, and DNS tracking to identify who could be safely impersonated without risk of in-person exposure.
The attack itself used a technique we pioneered called “email seeding.” By sending innocuous emails from the impersonation target’s doppelganger address (“did you get my last email?”), we planted the fake address in recipients’ email auto-complete caches. When the Director of IT Security later tried to email the real security manager, his email client auto-completed to our address, delivering an incident report directly to us.
We weaponized that trust relationship by embedding a zero-day Microsoft Word exploit with our custom malware (RADON) into a document and returning it to the target. Within 10 minutes of delivery, we had covert control of a corporate desktop. Using keylogger captures and screenshots, we harvested TeamViewer credentials and discovered that a third-party IT support company had deployed TeamViewer across the casino’s entire server infrastructure with stored credentials. Within 30 minutes of initial access, we had more control over the casino’s network than its own IT department.
The engagement tested the casino’s defenses against realistic adversary tradecraft, from initial reconnaissance through social engineering, exploitation, and lateral movement. Our findings provided the contextualized threat intelligence they needed to establish concrete threat informed defenses.
Building Threat-Informed Defenses Through Contextualized Threat Intelligence
Learning about what vulnerabilities exists provides some insight into what could go wrong. Contextualized threat intelligence from TLPT tells you what is most likely to go wrong before it does and enables you to do something about it before you suffer a breach.
Why Context Changes Everything
A vulnerability in your web application carries different risk depending on who wants to exploit it. A healthcare organization faces different adversaries than a hedge fund. A company with extensive cloud infrastructure faces different attack vectors than one running legacy on-premises systems.
Contextualized threat intelligence transforms raw threat data into organization-specific insights by considering:
- Industry-specific risks: The financial sector, healthcare, and critical infrastructure each face distinct threat actor profiles
- Geographic factors: Regulatory environments, regional threat actors, and geopolitical considerations
- Infrastructure characteristics: Cloud vs. on-premises, third-party dependencies, remote workforce considerations
- Business operations: Critical functions, data flows, and process interdependencies
Moving Beyond Automated Scanning
Most penetration testing vendors deliver little more than vetted automated vulnerability scans (or AI based penetration tests) that masquerade as penetration tests. This is like running a fire drill with the alarms disabled and no smoke, everything looks fine until there’s an actual fire. It establishes a dangerous false sense of security.
Automation based testing finds some known vulnerabilities and might even do basic chaining. Threat actors, on the other hand, chain multiple weaknesses in complex and novel ways, they exploit business logic flaws, manipulate human behavior with social engineering, and regularly uncover vulnerabilities that are unique to their victim.
Genuine penetration testing, the kind that delivers real security value, requires experienced and creative human operators. It leverages creativity and intuition that cannot be replicated by technology, not even AI. TPLT delivers real value because it structures the entire engagement around realistic threat scenarios and not pre-defined check in the box exercises.
Sources Behind Our Threat-Informed Approach
Real threat intelligence is not easy to come by. The best source comes from combined effort of ongoing intelligence gathering and leveraging data aggregators. Many data aggregators collect records that were stolen during third party data breaches. Those records are often packaged in ways that provide insight into threat actor behavior, communication, malware, etc.
Additional sources include:
- Active threat actor tracking and attribution research
- Industry-specific threat reports and incident data
- Dark web monitoring for targeting indicators
- Technical intelligence on current attack tooling and infrastructure
- Geopolitical analysis affecting cyber threat landscapes
This intelligence directly shapes testing scope, attack scenarios, and success criteria.
How TLPT Supports DORA and Regulatory Readiness
The Digital Operational Resilience Act (DORA) took effect on January 17, 2025, establishing uniform requirements for ICT risk management across the European Union’s financial sector. TLPT under DORA is a core component of advanced testing requirements.
Aligning TLPT with DORA Requirements
DORA mandates TLPT for significant financial entities with mature Information and Communication Technology (ICT) systems. Key requirements include:
- Frequency: TLPT must be conducted every three years at a minimum, though supervisory authorities may require more frequent testing
- Scope: Testing must cover critical live production systems and include ICT third-party service providers where relevant
- Purple teaming: Collaborative exercises between TLPT teams and blue teams are mandatory under DORA
- External threat intelligence: The threat intelligence provider must always be external to the financial entity
- Tester qualifications: DORA specifies minimum experience requirements and professional certifications for testing teams
Preparing for TLPT Under DORA
Organizations preparing for TLPT should:
- Identify critical functions and systems: Map the ICT processes, systems, and technologies that support critical business functions. This becomes the foundation for testing scope.
- Assess third-party dependencies: DORA requires that relevant ICT third-party providers participate in TLPT. This requires contractual provisions and coordination.
- Establish a control team: A small internal group manages the TLPT process, maintains confidentiality, and coordinates with regulators.
- Engage qualified providers: Select threat intelligence providers and red team testers who meet DORA’s specific qualification requirements.
- Plan for purple teaming: Build time and resources for the collaborative phase where findings translate into defensive improvements.
- Document everything: DORA requires comprehensive reporting to supervisory authorities, including test results, identified weaknesses, and remediation plans.
How to Choose a Threat-Led Penetration Testing (TLPT) Partner You Can Trust
Not every penetration testing vendor is capable of performing TLPT. The technical depth, threat intelligence capabilities, and regulatory knowledge required exceed what most firms deliver. We wrote a whitepaper to help organizations select a penetration testing vendor that best meets their needs. The paper was featured in Forbes and recently updated.
Verify Qualifications and Experience
DORA Article 27 specifies that TLPT testers must:
- Demonstrate the highest suitability and reputability
- Possess technical and organizational capabilities with specific expertise in threat intelligence, penetration testing, and TLPT
- Hold certifications from recognized accreditation bodies (CREST, OSCP, and similar credentials)
- Provide independent assurance regarding risk management practices
- Carry professional indemnity insurance covering misconduct and negligence
Specifically, the team must include:
- A manager with at least five years of penetration testing and TLPT experience
- At least two additional testers, each with minimum two years of experience
- Combined participation in at least five previous engagements related to penetration testing and TLPT
Evaluate Threat Intelligence Capabilities
The threat intelligence driving TLPT must be current, relevant, and specific to your organization. Ask potential vendors:
- How do you gather and validate threat intelligence?
- Can you demonstrate industry-specific threat expertise?
- How do you contextualize intelligence to our organization’s risk profile?
- What sources inform your threat actor profiles and attack scenarios?
Remember: DORA requires the threat intelligence provider to be external. If your TLPT vendor also provides threat intelligence, verify they meet independence requirements.
Why Choose Netragard for TLPT?
Since 2006, Netragard has delivered Realistic Threat Penetration Testing (called TLPT today) that emulates real-world attacker behavior, not automated scans dressed up in technical jargon. Our reputation is based on our ability to provide realistic tests and deliver real value with a high ROI.
Our approach to TLPT combines:
Contextualized Threat Intelligence
We build attack scenarios from current threat actor research, industry-specific intelligence, and deep analysis of your organization’s unique risk profile. Testing reflects genuine threats, not generic checklists.
Real Time Dynamic Testing™
Our proprietary methodology adapts in real time based on what we discover during engagements. Like actual adversaries, we adjust tactics based on your environment rather than following predetermined scripts. [Learn more about Real Time Dynamic Testing]
Expert Human Testers
Our team brings decades of combined experience in vulnerability research, exploit development, and red team operations. We find the business logic flaws, complex attack chains, and vulnerabilities unique to your systems that automated tools miss. [Explore our penetration testing services]
Regulatory Alignment
We understand DORA requirements and work with many financial institutions to meet compliance obligations while delivering security value beyond checkbox testing.
Actionable Results
Our reports tell you exactly what happened, what it means, and what to do about it. We support purple team exercises and remediation validation to ensure findings translate into stronger defenses.
FAQ
What is contextualized threat intelligence?
Contextualized threat intelligence transforms generic threat data into organization-specific insights by considering industry, geography, infrastructure, and business operations. A vulnerability carries different risk depending on who wants to exploit it. Contextualization answers: Which threat actors target organizations like ours? What attack vectors do they use? What are their objectives? This context ensures TLPT scenarios reflect genuine risks rather than generic possibilities.
Is Threat-Led Penetration Testing different from red teaming?
TLPT is a specific and regulated type of testing that overlaps Red Teaming in many ways but is in fact different. Red Teaming gives testers flexibility to use whatever methods suit the environment. TLPT is more structured, attack scenarios must be based on documented threat intelligence about real threat actors. TLPT also includes mandatory components like purple teaming (under DORA) and specific tester qualification requirements that standard red team engagements may not require. Red teaming is typically mission focused with well-defined objectives and operates at higher levels of threat.
Is TLPT required under DORA regulations?
Yes, for certain financial entities. DORA mandates TLPT for significant financial institutions with mature ICT systems. The requirement applies to banks, insurers, investment firms, and other financial entities deemed systemically important or possessing sufficiently mature cyber defenses. Regular penetration testing and vulnerability assessments are required for all in-scope firms, but TLPT obligations apply only to designated entities. Supervisory authorities determine which organizations must conduct TLPT.
How often should organizations conduct TLPT?
DORA requires TLPT at least every three years, though supervisory authorities may mandate more frequent testing based on risk profiles or changing threat landscapes. Organizations should use the time between TLPT cycles to prepare—mapping critical functions, establishing control teams, and engaging qualified vendors. Between TLPT cycles, regular penetration testing and continuous security monitoring remain essential.
What is the main difference between TLPT and Penetration Testing?
Industry standard penetration testing uses a checklist methodology to identify known vulnerabilities across your environment. TLPT takes a fundamentally different approach: it begins with intelligence about the threat actors targeting your industry, models their tactics and techniques, then tests your defenses against those realistic attack scenarios. The result is actionable insight into how you’d actually be compromised and what controls can be used to stop it.