Key Takeaways:
GLBA applies more broadly than many organizations assume. It covers a wide range of businesses engaged in financial activities, and the Safeguards Rule is the part that creates the core operational security requirements.
For most covered institutions, annual penetration testing is mandatory. Under 16 CFR 314.4, organizations without effective continuous monitoring must perform annual penetration testing and vulnerability assessments at least every six months.
Vulnerability scanning alone does not satisfy the rule’s intent. The Safeguards Rule separates penetration testing from vulnerability assessments, signaling that regulators expect testing that validates real-world exploitability rather than just automated findings.
GLBA compliance now includes stronger governance and breach-readiness expectations. Covered institutions must maintain a documented security program, oversee service providers, and report qualifying breaches involving 500 or more consumers to the FTC within 30 days of discovery.
What Is the GLBA and Why It Exists
Overview of the Gramm-Leach-Bliley Act
The Gramm-Leach-Bliley Act (GLBA) is a federal law enacted in 1999 that requires financial institutions to explain how they share and protect customer information. The law applies far more broadly than most organizations realize. If your business is significantly engaged in financial activities, lending, insurance, investment advising, tax preparation, debt collection, or even auto financing, GLBA applies to you. It is not limited to banks and credit unions.
GLBA established three core requirements: the Financial Privacy Rule governing how institutions collect and share personal financial information, the Safeguards Rule requiring institutions to maintain an information security program, and pretexting protections that prohibit fraudulent access to personal data. For security professionals and the organizations they protect, the Safeguards Rule is where the operational obligations live.
GLBA Security Rule Explained
The GLBA Safeguards Rule (16 CFR 314) requires financial institutions to develop, implement, and maintain a comprehensive information security program that includes administrative, technical, and physical safeguards designed to protect customer information. The FTC issued the original rule in 2001 but substantially revised it in 2021 with enforcement beginning in 2023. The revised rule replaced vague guidance with specific, prescriptive requirements including designated security personnel, risk assessments, access controls, encryption, incident response, and mandatory penetration testing.
The Safeguards Rule applies to any institution that maintains customer information for 5,000 or more consumers. Smaller institutions are exempt from certain prescriptive requirements but must still maintain a security program appropriate to their size and risk.
GLBA Penetration Testing Requirements for 2026
Does GLBA Require Penetration Testing?
Yes. Section 314.4(d)(2) of the revised Safeguards Rule explicitly requires either continuous monitoring or periodic penetration testing and vulnerability assessments. The language is direct: absent effective continuous monitoring, institutions must conduct annual penetration testing of information systems determined each given year based on relevant identified risks, and vulnerability assessments at least every six months.
Most financial institutions do not have continuous monitoring capabilities that satisfy the FTC’s threshold. That means annual penetration testing for GLBA is not optional. It is a regulatory mandate. The scope must cover all information systems where nonpublic personal information (NPI) is stored, processed, or transmitted. This includes internal networks, customer-facing applications, and third-party integrations that handle customer data.
Annual Penetration Testing Expectations Under the Safeguards Rule
The Safeguards Rule requires that penetration testing be conducted at least annually and whenever there are material changes to operations or business arrangements that could affect the security of customer information. This includes new system deployments, significant infrastructure changes, mergers, and major software updates.
The FTC expects testing that reflects actual risk, not checkbox compliance. A genuine penetration test maps the Paths to Compromise through your environment, demonstrating how an attacker would move from initial access to your most sensitive customer data. This produces contextualized threat intelligence that informs remediation priorities and defensive measures. An automated vulnerability scan repackaged as a penetration test does not satisfy the intent of the rule, and it will not protect you when the FTC comes asking questions after a breach.
Why Vulnerability Scanning Alone is Not Enough
The Safeguards Rule distinguishes between penetration testing and vulnerability assessments for a reason. Vulnerability scanning identifies known weaknesses across your environment. It tells you what might be exploitable. Penetration testing proves what is exploitable by actively attempting to compromise systems the way a real attacker would. Scanning finds the unlocked doors. Penetration testing walks through them, maps the path to your vault, and shows you what an attacker would take.
The revised Safeguards Rule requires both: annual penetration testing and vulnerability assessments at least every six months. Treating a vulnerability scan as a substitute for a penetration test is a compliance gap that regulators and auditors will identify. More importantly, it leaves your organization exposed to the exact attack scenarios that genuine testing would have revealed.
The 5 Essential GLBA Cybersecurity Requirements
The Safeguards Rule establishes five core obligations that every covered institution must address:
Identify and Assess Risks
Section 314.4(b) requires a written risk assessment that identifies reasonably foreseeable internal and external risks to the security, confidentiality, and integrity of customer information. The risk assessment must evaluate the sufficiency of existing safeguards and must be updated periodically, particularly when changes to operations, systems, or threat landscape warrant reassessment. This is not a theoretical exercise. It is the foundation that determines the scope of your penetration testing, the controls you implement, and the monitoring you deploy.
Implement Safeguards
Based on the risk assessment, institutions must implement safeguards that address identified risks. The revised rule specifies concrete requirements: access controls limiting who can access customer information, encryption of data in transit and at rest, secure development practices for in-house applications, multi-factor authentication for anyone accessing customer information, and procedures for secure disposal of customer data. These are not suggestions. They are regulatory requirements with specific enforcement mechanisms.
Test and Monitor Controls
This is where penetration testing lives within the GLBA framework. Section 314.4(d) requires institutions to regularly test or monitor the effectiveness of safeguards. The rule mandates either continuous monitoring or a combination of annual penetration testing and bi-annual vulnerability assessments. Testing must be risk-informed, covering the systems most critical to customer data protection. Results must drive remediation, and remediation must be documented.
That phrase, “test the effectiveness of safeguards,” deserves careful attention because most organizations misunderstand it. Testing effectiveness does not mean running a scanner against your systems to confirm that patches are installed and firewalls are configured. It means subjecting your defenses to the same caliber of attack they are supposed to withstand. If your safeguards are designed to protect customer data from sophisticated threat actors, then testing their effectiveness requires attacking them with the same techniques, creativity, and persistence that those threat actors would bring, something automation cannot do.
Very few penetration testing companies operate at this level. The industry is saturated with providers who run automated scans, reformat the output into a report, and call it a penetration test. That approach might check a compliance box, but it does not test the effectiveness of anything. Advanced persistent threats do not limit themselves to what scripts can find, and neither should your testing program. If the Safeguards Rule requires you to test the effectiveness of your safeguards, the testing must reflect the threat. Otherwise, you are measuring your defenses against a standard no real attacker is constrained by.
Train Employees
Section 314.4(e) requires security awareness training for all personnel. Training must be updated to reflect current threats and must occur at hire and periodically thereafter. The training obligation extends beyond IT staff. Every employee who handles customer information or has access to systems that store it must understand their security responsibilities. Social engineering and phishing remain the most effective initial access vectors, and no amount of technical controls compensates for untrained staff.
Organizations that pair training with accountability see measurably better security outcomes. That means clear policies with defined consequences for violations: clicking through phishing simulations repeatedly without improvement, sharing credentials, bypassing access controls, or ignoring data handling procedures. When employees understand that security expectations carry the same weight as other job performance metrics, behavior changes. When there are no consequences, training becomes background noise that people sit through and forget.
Oversee Service Providers
Section 314.4(f) requires institutions to oversee service providers that access or maintain customer information. This means contractual security requirements, due diligence during vendor selection, and periodic assessment of vendor security practices. If a third-party processor is breached because of inadequate security, your institution bears the regulatory and reputational consequences. The Safeguards Rule makes vendor oversight your responsibility, not a courtesy.
Penetration testing supports this obligation directly. Testing your own environment reveals how third-party integrations interact with your systems and whether those connections introduce exploitable weaknesses. If a vendor’s API handles customer data with insufficient authentication, or if their integration creates an unintended lateral movement path into your network, a genuine penetration test will find it. You cannot rely on a vendor’s self-reported security posture to protect your customers. You need to verify how their access actually behaves within your environment.
Open-source intelligence (OSINT) adds another layer of vendor oversight that most institutions overlook. Before signing a contract, OSINT research can reveal whether a vendor has suffered previous breaches, whether their infrastructure exposes sensitive services to the internet, whether their employees are leaking credentials on public repositories, or whether their security practices match what their sales team promised. This is not hypothetical. Breach databases, exposed code repositories, misconfigured cloud storage, and leaked credentials are publicly discoverable for organizations that know where to look. Conducting OSINT on your service providers before and during the relationship gives you visibility into risks that no questionnaire or SOC 2 report will surface.
GLBA Compliance Checklist for 2026
Use this checklist as a framework to evaluate your institution's readiness under the revised Safeguards Rule.
Documentation Requirements
Testing and Monitoring Items to Include in Your GLBA Checklist
Required Updates to Your Security Program
Breach Notification Readiness
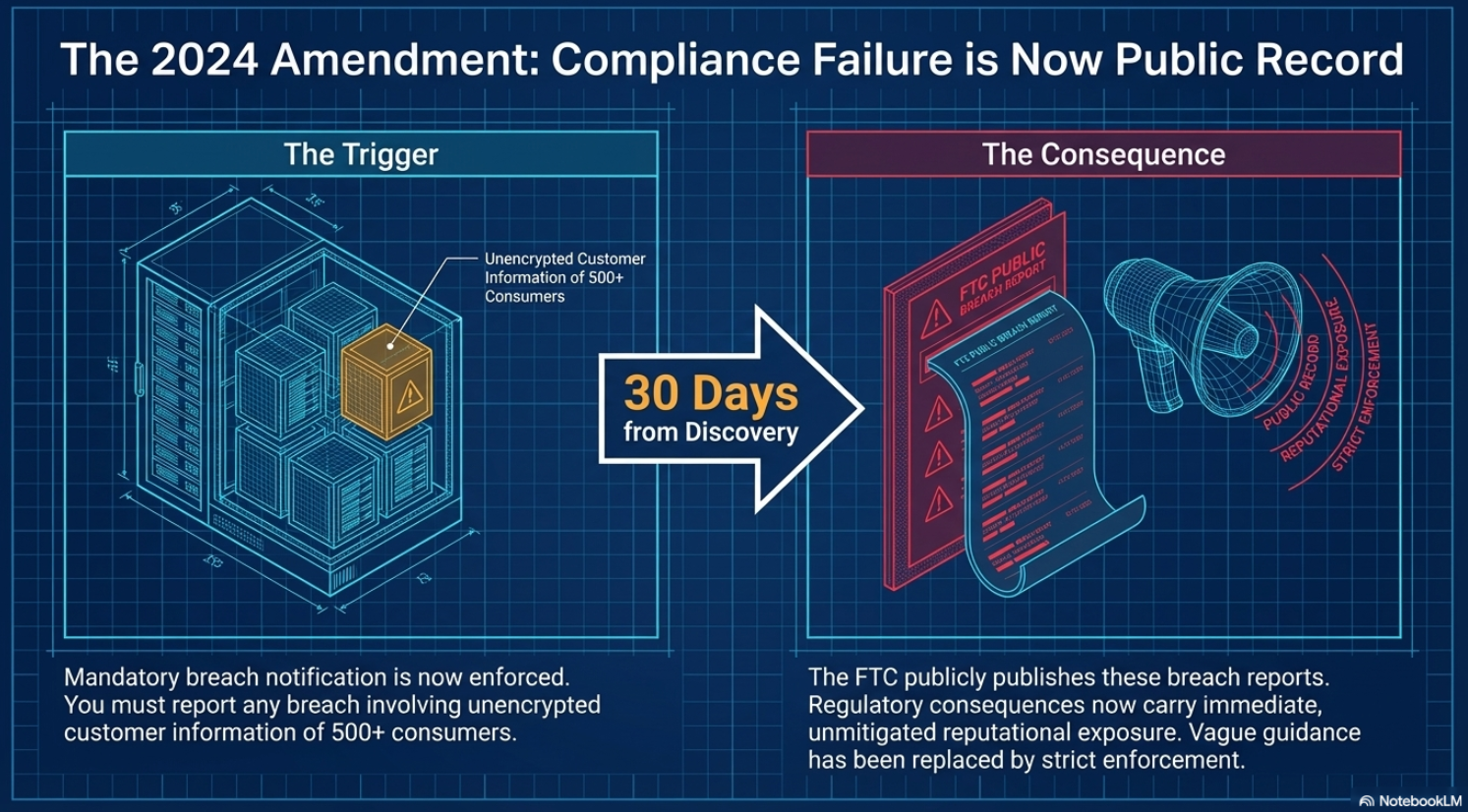
The 2024 amendment to the Safeguards Rule added mandatory breach notification requirements. Institutions must report to the FTC within 30 days of discovering any breach involving unencrypted customer information of 500 or more consumers. The FTC publishes these reports publicly, meaning regulatory consequences now include immediate reputational exposure.
- Breach detection and classification procedures documented and tested
- FTC notification process defined with 30-day reporting timeline
- Consumer notification procedures in place for affected individuals
- Forensic investigation capabilities identified, whether internal or through a retained third party
- Legal review process for breach determination and notification obligations
How to Prepare for a GLBA Security Audit
Audit preparation begins with documentation, not last-minute testing. Auditors and regulators evaluate your security program as a whole: the risk assessment, the controls derived from it, the testing that validates those controls, and the evidence that findings drive remediation. A penetration test report alone does not demonstrate compliance. The report must connect to your risk assessment, your remediation process must be documented, and retesting must confirm that fixes work.
- Start by reviewing your written security program against the current Safeguards Rule requirements.
- Verify that your Qualified Individual is designated and actively reporting to the board.
- Confirm that your risk assessment reflects your current environment, not the environment you had when you last updated it.
- Ensure that penetration testing and vulnerability assessments have been conducted on schedule and that findings have been remediated and retested.
The institutions that struggle with audits are the ones that treat compliance as an annual event. The ones that pass without difficulty have integrated these requirements into their operations: continuous documentation, regular testing, and a security program that evolves with their risk profile.
Why Financial Institutions Choose Netragard for Penetration Testing
Financial institutions face regulatory scrutiny that demands more than superficial testing. A scan repackaged as a penetration test will not survive an FTC audit, and it will not protect your customers. Netragard has provided genuine penetration testing services to financial institutions since 2006. Our testers map the actual Paths to Compromise through your environment, demonstrating exactly how an attacker would reach your customer data. The result is contextualized threat intelligence that satisfies regulatory requirements and gives you actionable intelligence to strengthen your defenses.
Our reports document each finding with reproduction steps, risk ratings aligned to your business context, and remediation guidance specific to your environment. We provide the evidence your Qualified Individual needs to report to the board and the detail your team needs to fix what matters. We retest for free within 60 to 90 days to verify remediation, giving you documented proof that identified risks have been addressed.
If your institution needs penetration testing that meets the Safeguards Rule’s requirements and actually protects your customers, Request a Quote to discuss your compliance and security needs.
FAQ
What is the purpose of GLBA?
The Gramm-Leach-Bliley Act requires financial institutions to protect the privacy and security of customer information. It establishes rules for how institutions collect, share, and safeguard personal financial data. The Safeguards Rule, enforced by the FTC, mandates that covered institutions maintain a comprehensive information security program with specific administrative, technical, and physical controls.
What is GLBA 501(b)?
Section 501(b) of the GLBA directed federal banking regulators to establish standards requiring financial institutions to implement administrative, technical, and physical safeguards to protect the security, confidentiality, and integrity of customer information. This section is the statutory authority behind the Interagency Guidelines and the FTC’s Safeguards Rule. It requires that safeguards protect against anticipated threats, prevent unauthorized access, and ensure the security of customer information maintained by or on behalf of the institution.
Does GLBA require penetration testing?
Yes. The revised Safeguards Rule (Section 314.4(d)(2)) requires institutions to conduct either continuous monitoring or annual penetration testing combined with vulnerability assessments at least every six months. For most institutions that lack continuous monitoring capabilities, annual penetration testing is a mandatory compliance requirement. The testing must cover all information systems that store, process, or transmit nonpublic personal information.
How often should GLBA safeguards be tested?
The Safeguards Rule requires annual penetration testing and vulnerability assessments at least every six months. Testing must also be conducted whenever there are material changes to operations, systems, or business arrangements that could affect the security of customer information. Organizations should view these as minimum frequencies. Institutions with higher risk profiles, rapid growth, or frequent system changes should consider more frequent testing to maintain genuine security.