Key Takeaways:
SOC 2 does not explicitly require penetration testing, but in 2026 most auditors expect it as practical evidence that CC4.1 and related security controls are actually working, especially for Type II audits.
An effective SOC 2 penetration test must align tightly to your SOC 2 system boundary, map findings to relevant Trust Services Criteria (such as CC4.1, CC6.1, CC7.1–CC7.4), occur within the audit period, and include clear remediation and retest evidence.
Automated scanners and AI-only PTaaS are not sufficient; auditors look for human-driven, adversarial testing that can uncover business logic issues, chained exploits, and provide risk-based context, not just raw vulnerability lists.
- Organizations are expected to cover all in-scope attack surfaces (external and internal networks, web apps, APIs, and cloud environments) at least annually and after major changes.
Organizations pursuing SOC 2 compliance often ask whether the framework actually requires penetration testing. The short answer: technically no, but practically yes. Understanding this distinction will determine whether your audit proceeds smoothly or runs into costly delays.
Understanding SOC 2 and Its Security Expectations
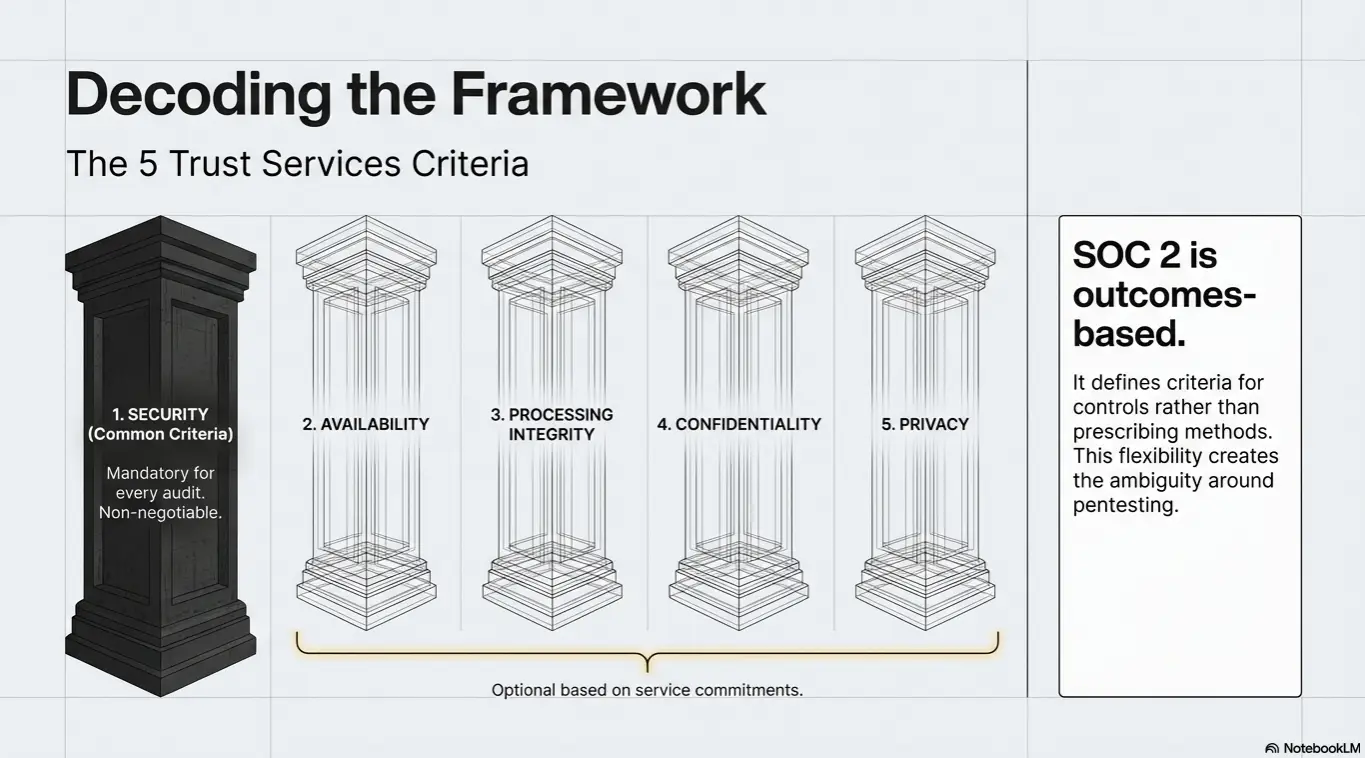
SOC 2, developed by the American Institute of Certified Public Accountants (AICPA), provides a framework for service organizations to demonstrate they protect customer data. Unlike prescriptive compliance frameworks that mandate specific security measures, SOC 2 is outcomes-based, meaning it defines criteria your controls must meet rather than dictating exactly how to meet them.
The framework evaluates organizations against five Trust Services Criteria:
- Security (Common Criteria): Mandatory for every audit. Covers access management, risk assessment, change management, incident response, and protection against unauthorized access.
- Availability: Uptime commitments, disaster recovery, and SLA enforcement.
- Processing Integrity: Whether data processing is complete, accurate, timely, and authorized.
- Confidentiality: Protecting non-personal confidential information such as trade secrets or source code.
- Privacy: Personal information handling according to AICPA’s Generally Accepted Privacy Principles.
Organizations include criteria based on their service commitments and contractual obligations. This flexibility creates latitude in how you demonstrate control effectiveness, but also creates ambiguity around penetration testing expectations.
Does SOC 2 Require Penetration Testing in 2026?
The Official SOC 2 Position
Technically, no. SOC 2 does not explicitly mandate penetration testing. The AICPA’s Trust Services Criteria provides guidelines but allows organizations flexibility in demonstrating that security controls are present and functioning.
However, the framework strongly implies the need for rigorous security validation. Common Criteria 4.1 (CC4.1) states: “The entity selects, develops, and performs ongoing and/or separate evaluations to ascertain whether the components of internal control are present and functioning.” The accompanying points of focus specifically reference penetration testing as one method to satisfy this requirement—and it is often perceived as the best method.
What Auditors Expect During Type I and Type II Engagements
While penetration testing may not appear on a formal checklist, the reality in 2026 is that auditors overwhelmingly expect to see penetration testing evidence.
During Type I engagements, auditors evaluate control design at a specific point in time. During Type II audits, they review both design and operating effectiveness over a period, usually six to twelve months. For Type II examinations, a penetration test provides tangible evidence that your security controls function under adversarial conditions.
Auditors aren’t simply looking for policy documentation. They want proof that someone has actually attempted to bypass your controls and documented what they found.
Why Automated Scans Are Not Sufficient for Compliance
Many organizations attempt to satisfy SOC 2 security validation requirements using automated vulnerability scanners, AI Penetration Testing as a Service (PTaaS), or compliance-focused penetration testing. While these are often marketed as capable services, they do not operate at real adversarial levels and may fail to deliver the evidence auditors expect.
The problems are threefold:
Limited scope. Automated scanners identify some known vulnerabilities but cannot evaluate business logic flaws, chained attack scenarios, or complex authorization bypass techniques that manual testing uncovers. They also generate high rates of false positives and false negatives that degrade report accuracy.
Missing context. Scanner-heavy reports lack the contextual analysis auditors need. A vulnerability scan might flag hundreds of findings without explaining which ones pose genuine risk to systems within your SOC 2 scope. This forces auditors to question whether your organization truly understands its security posture.
Auditor rejection. Auditors may reject assessments that rely heavily on automated tools, including autonomous AI pentesting platforms. The distinction between genuine penetration testing and automated testing or scanning isn’t semantic, it’s significant. Genuine penetration testing emulates how real attackers operate. Automated testing does not and cannot.
This distinction matters when you consider return on investment. Quality penetration testing that prevents even a single breach pays for itself many times over. With the average cost of a data breach reaching $4.88 million in 2024, a $40,000 engagement that prevents a single breach represents an ROI approaching 12,000%. Checkbox testing, by contrast, creates a false sense of security while leaving real vulnerabilities in place. This becomes a true negative ROI that compounds as undetected weaknesses persist until an actual adversary exploits them.
SOC 2 Penetration Testing Requirements for 2026
Alignment with Trust Services Criteria

Effective SOC 2 penetration testing must map directly to the Trust Services Criteria relevant to your audit scope. At minimum, this means addressing:
- CC4.1 – Monitoring Activities: Regular penetration tests demonstrating that you evaluate security control efficacy.
- CC7.1 – System Operations: Validation that procedures detect configuration changes introducing risk.
- CC6.1 – Logical and Physical Access: Verification that access controls cannot be bypassed.
- CC7.2–CC7.4 – Security Events & Incident Response: While not strictly required, we strongly recommend validating detection and response capabilities. This provides evidence that your organization can identify and contain threats—not just prevent them.
Scope Definition Requirements
Your penetration test scope must include all systems, applications, and infrastructure within your SOC 2 boundary: production environments, customer-facing applications, APIs, and supporting infrastructure that processes, stores, or transmits customer data.
Auditors will compare your penetration test scope against your SOC 2 system description. Misalignment raises immediate concerns about whether you’ve adequately evaluated your security controls.

Testing Frequency and Timing
Industry best practice calls for penetration testing at minimum annually, with additional testing following significant system changes. For SOC 2 Type II audits, your most recent penetration test should fall within the audit observation period.
Organizations making substantial infrastructure changes, like migrating to new cloud platforms, deploying major application updates, or integrating new third-party services, should conduct targeted testing following those changes rather than waiting for the annual assessment.
Remediation Evidence Requirements
Auditors expect clear documentation showing that identified findings were remediated and that fixes were effective. Penetration testing vendors typically perform follow-up testing focused on re-exploiting previously reported vulnerabilities. If those weaknesses can no longer be exploited, they’re marked as resolved.
Your vendor will deliver a remediation report reflecting verified fixes. Maintaining a well-defined remediation timeline with documented status updates demonstrates that your organization treats findings seriously and has mature processes to identify, prioritize, and close security gaps.
Required Types of Penetration Testing for SOC 2
The type of testing your organization needs depends on your objectives and what falls within your SOC 2 scope. The following are the most common types used for SOC 2 compliance.
External Network Testing
External infrastructure testing evaluates your internet-facing systems, like web servers, email servers, API servers, etc. by emulating attacks from threat actors. This provides insight into what an attacker sees when targeting your organization from the internet.
For SOC 2, external penetration testing provides evidence that perimeter defenses can withstand attacks from adversaries operating within the context of your industry.
Internal Network Testing
Internal infrastructure testing evaluates systems behind your perimeter, like desktops, printers, internal servers, and cloud environments by emulating attacks from threat actors who have bypassed perimeter defenses (including rogue employees). This testing reveals the efficacy of internal detection and response capabilities.
For SOC 2, internal testing provides evidence that controls adequately limit damage and safeguard data confidentiality, integrity, and availability.
Web Application Security Testing
Web applications are among the top targets for threat actors seeking sensitive data. Web application penetration testing emulates the techniques, tactics, and procedures (TTPs) attackers use to bypass controls and capture data. At minimum, testing should cover the OWASP Top-10:
- A01 Broken Access Control
- A02 Cryptographic Failures
- A03 Injection
- A04 Insecure Design
- A05 Security Misconfiguration
- A06 Vulnerable and Outdated Components
- A07 Identification and Authentication Failures
- A08 Software and Data Integrity Failures
- A09 Security Logging and Monitoring Failures
- A10 Server-Side Request Forgery
For SOC 2, web application testing provides evidence that applications are robust enough to protect data confidentiality, integrity, and availability.
API Penetration Testing
APIs drive most modern web and mobile applications. When you perform online banking, the website sends and receives data through APIs and presents it in human-readable form. Because APIs do the real computing work, API penetration testing is often conducted alongside web and mobile application testing.
API testing should provide coverage for the OWASP API Security Top-10:
- API1 Broken Object Level Authorization
- API2 Broken Authentication
- API3 Broken Object Property Level Authorization
- API4 Unrestricted Resource Consumption
- API5 Broken Function Level Authorization
- API6 Unrestricted Access to Sensitive Business Flows
- API7 Server Side Request Forgery
- API8 Security Misconfiguration
- API9 Improper Inventory Management
- API10 Unsafe Consumption of APIs
For SOC 2, API penetration testing provides evidence that APIs are robust enough to protect data.
Cloud Infrastructure Testing for AWS, Azure, and GCP
Cloud security assessments ensure that systems and data in cloud environments don’t introduce unidentified risks. Unlike traditional penetration testing, cloud assessments focus on configuration review and architecture analysis rather than active exploitation because many security controls are maintained by the cloud provider and cannot be tested directly.
Cloud deployments operate under a shared responsibility model:
- Infrastructure as a Service: You manage everything from the operating system up.
- Platform as a Service: You manage applications and data.
- Software as a Service: You manage data and access controls.
For SOC 2, cloud assessments provide evidence that your cloud configuration meets security requirements and doesn’t introduce gaps that could compromise data.
Additional Testing Considerations
Depending on your environment and SOC 2 scope, additional testing types may be warranted: mobile application security testing, Wi-Fi penetration testing, social engineering assessments, and others. The specific mix depends on your threat landscape and what systems fall within scope.
Tips for Preparing for SOC 2 Penetration Testing in 2026
A few key points distinguish SOC 2 penetration testing from standard security assessments:
Scope alignment is paramount. A SOC 2 penetration test must evaluate systems within your defined SOC 2 boundary. Testing systems outside this scope provides interesting security information but doesn’t directly support your audit.
Control mapping connects findings to criteria. Reports should articulate which controls were validated and how testing activities addressed CC4.1, CC7.1, and other relevant criteria.
Auditor-ready documentation matters. Reports should include an executive summary for management, detailed technical findings with severity ratings, remediation recommendations, and evidence of retesting.
Beyond understanding the differences, here are practical steps to prepare:
- Define your scope clearly before engaging a testing provider. Document which systems fall within your SOC 2 boundary and ensure your penetration testing scope mirrors this definition.
- Schedule testing within your audit window. For Type II audits, a test conducted outside your observation period provides limited value.
- Plan remediation time. Budget adequate time between testing completion and audit fieldwork to address findings.
- Establish clear communication channels. Your testing provider should have direct access to technical contacts who can answer questions during the engagement.
- Review provider qualifications. Effective SOC 2 penetration testing requires providers with compliance experience who understand what auditors need, not just technical testing skills.
- Request sample reports. Evaluate whether the provider’s deliverables meet your auditor’s expectations for evidence documentation.
SOC 2 Penetration Testing Checklist for 2026
Pre-Engagement Preparation
- Document all systems within SOC 2 scope boundary
- Identify external network ranges and IP addresses in scope
- List all web applications and APIs requiring testing
- Document cloud environments (AWS, Azure, GCP) and configurations
- Confirm testing timeline falls within audit observation period
- Establish points of contact for testing coordination
Provider Selection
- Verify provider experience with SOC 2 compliance testing
- Confirm testing methodology is threat-led, not scanner-dependent
- Review sample reports for auditor-ready documentation
- Validate credentials and certifications
Testing Execution
- Confirm scope coverage matches SOC 2 system boundary
Post-Test Activities
- Review findings and severity ratings with testing team
- Develop remediation plan with assigned owners and deadlines
- Document remediation evidence and completion dates
- Request retest validation for all findings
- File complete report and supporting evidence for auditor review
Why Organizations Choose Netragard for SOC 2 Penetration Testing

Netragard delivers genuine, threat led penetration testing, not repackaged vulnerability scans dressed up as security assessments.
Our Real Time Dynamic Testing methodology combines deep technical expertise with contextualized threat intelligence. Every engagement is tailored to your specific environment, threat landscape, and compliance requirements. Our testers operate as real-world adversaries, ethically, legally, and within scope boundaries, while maintaining the documentation discipline auditors expect.
We understand that SOC 2 penetration testing serves dual purposes: validating your security controls and providing evidence for your audit. Our reports bridge technical findings with compliance requirements, mapping discoveries directly to Trust Services Criteria and providing clear remediation guidance.
With two decades of cybersecurity expertise, Netragard has supported organizations from emerging companies to Fortune 500 enterprises in demonstrating security control effectiveness. Our penetration testing goes beyond checkbox compliance to provide genuine assurance that your defenses work and Netragard is seen as a top rated penetration testing company.
FAQ
What are SOC 2 compliance requirements?
SOC 2 compliance requires implementing and maintaining controls aligned with the AICPA’s Trust Services Criteria. The Security criteria is mandatory, covering control environment, risk assessment, access controls, system operations, and change management. Additional criteria like Availability, Processing Integrity, Confidentiality, and Privacy may be included based on your service commitments. Compliance is demonstrated through an audit conducted by an independent CPA firm.
What are the 5 criteria for SOC 2?
The five Trust Services Criteria are: (1) Security: protecting systems against unauthorized access; (2) Availability: ensuring systems are accessible as promised; (3) Processing Integrity: verifying processing is complete, accurate, and authorized; (4) Confidentiality: protecting confidential information; and (5) Privacy: handling personal information appropriately. Security is required for every audit; the others are optional based on your commitments.
Is SOC 2 compliance mandatory?
SOC 2 is not legally mandatory. Unlike HIPAA or GDPR, no governmental authority requires SOC 2 attestation. However, it has become a de facto requirement for service organizations, particularly SaaS companies, because customers increasingly demand SOC 2 reports before signing contracts. While voluntary legally, commercial reality makes SOC 2 essential for most organizations seeking enterprise customers.
Does SOC 2 require penetration testing?
Technically, no. Penetration testing is not explicitly mandated. However, it is strongly recommended and expected by most auditors as evidence supporting Common Criteria 4.1 (CC4.1), which requires evaluations to verify controls are present and functioning. Failing to provide penetration testing evidence often raises questions and may complicate the examination. While not required, you may face audit challenges without it.
Does SOC 2 cover GDPR?
No. SOC 2 and GDPR are separate frameworks with different objectives. SOC 2 is a voluntary attestation framework for service organization controls; GDPR is an EU regulation governing personal data protection with mandatory requirements. Some controls overlap around data security and privacy, but SOC 2 compliance does not satisfy GDPR requirements. Organizations subject to GDPR must address its obligations independently.
What is SOC 2 testing?
SOC 2 testing refers to procedures auditors perform during a SOC 2 examination to evaluate whether controls are designed appropriately and operating effectively. This includes reviewing policies, inspecting configurations, observing processes, and examining evidence. The term also encompasses security assessments organizations conduct themselves (including penetration testing and vulnerability scanning) to validate controls and prepare for their audit.