Key Takeaways:
Security intelligence, not tools, builds real defense. Most breaches go undetected not because organizations lack tools, but because they lack attacker-focused strategy. Real protection starts with understanding how an adversary would compromise your systems — not just collecting alerts.
Threat-led penetration testing is the foundation. A genuine, human-driven penetration test reveals Paths to Compromise that form the basis for precise defenses like honeypots and credential canaries — yielding higher impact than expensive SIEMs or automated scans.
Smart, targeted defense beats high-cost tech. With carefully deployed honeypots, credential canaries, and intelligence-driven segmentation, organizations can build enterprise-grade security for a fraction of the price — proving that smarter investments outperform larger budgets.
The average organization takes 194 days to detect a breach. Not because they lack security tools — most are already running six-figure SIEM platforms and around-the-clock security operations centers. They’re failing because the tools are not the problem. The strategy is.
At Netragard, we’ve spent years making the same argument: genuine security doesn’t start with a vendor’s feature list. It starts with one question — how would an attacker actually compromise your environment? The answer to that question, derived from real threat intelligence specific to your organization, is worth more than any enterprise platform you can buy.
Our founder and CEO Adriel Desautels recently laid out this framework in detail for SC Media. Below, we highlight the core approach and what it means for organizations operating on a realistic budget.
Start With a Threat-Led Penetration Test — Not a Scan
Everything in this framework begins with one investment: a real, human-driven penetration test. Not a scan. Not an automated tool. Not an AI-driven service. Skilled professionals who attempt to compromise your environment the same way a real attacker would — same Techniques, Tactics, and Procedures.
The output isn’t just a list of vulnerabilities. It’s contextualized threat intelligence: the exact Paths to Compromise from initial access to your most sensitive assets. That intelligence becomes the foundation for every defensive measure that follows. Expect to invest a minimum of $15,000 for a small organization. If a vendor quotes significantly less, they’re selling you a scan in disguise.
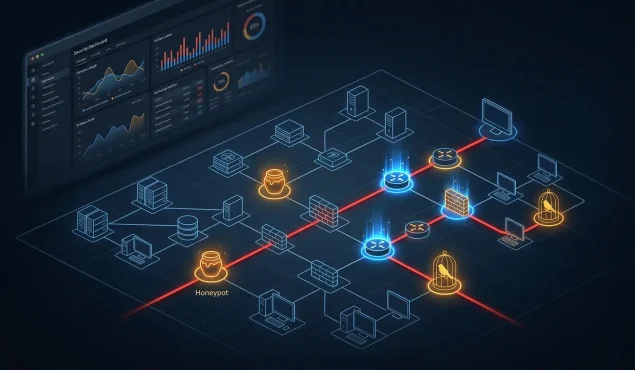
Deploy Honeypots in Cybersecurity — With Precision, Not Guesswork
Honeypots are inexpensive decoy systems with no production function — no legitimate user ever touches them. That’s what makes them uniquely powerful: zero false positives, zero security fatigue. Every alert is real.
Without a penetration test, honeypots are placed on assumptions. With one, they’re placed with precision — directly along the attack paths your testers already walked. You’re not guessing where attackers might go. You know, because skilled humans already took those exact routes.
The economics make the case on their own. A full honeypot deployment: $5,000–$20,000. A SIEM: $100,000–$500,000 annually. The honeypot, placed correctly, catches a lateral-moving attacker that the SIEM might flag 194 days later — or miss entirely.
Catch Lateral Movement Early With Credential Canaries
Credential theft is the engine of lateral movement. Attackers compromise one system, harvest credentials, and use them to reach the next. Your penetration test maps exactly where that happens in your environment.
Credential canaries exploit this behavior. Plant fake accounts, API keys, and password files in the exact locations where testers harvested real credentials. When an attacker uses one, you get an immediate, confirmed indicator of compromise — no legitimate user ever will. Cost to implement: nearly zero.
The Equifax Lesson: What Happens Without Intelligence-Driven Defense
In 2017, attackers exploited an unpatched Apache Struts vulnerability to breach a single Equifax web server. That wasn’t the catastrophe. What came next was.
They moved laterally for 76 days — through database after database, across 147 million personal records — while no honeypot tripped, no canary fired, and no segmentation stopped them. Final cost: $1.4 billion. The breach would likely have been contained to a single server if intelligence-driven defenses had been waiting along those paths. Not more expensive tools. Smarter ones.
The Full Framework, in Brief
The SC Media article lays out a complete approach for building a breach-ready posture at a fraction of the enterprise cost. The seven core measures:
- Commission a threat-informed penetration test to generate contextualized intelligence
- Map your attack paths and prioritize remediation based on real exploitability, not severity scores
- Deploy honeypots in cybersecurity along proven attack paths for zero-false-positive detection
- Plant credential canaries where testers harvested real credentials
- Validate and harden network segmentation based on demonstrated lateral movement routes
- Harden specific systems based on real exploit chains, not generic compliance checklists
- Run recurring validation cycles — defenses degrade, and annual pen testing keeps your intelligence current
The article also covers a dozen free and near-free measures any organization can implement immediately — from host-based firewalls and Group Policy hardening to credential monitoring and account lockout policies.
FAQ
Do I need expensive security tools to build strong defenses?
No. Most organizations already have more tools than they need. Real protection comes from understanding how attackers would actually compromise your systems and using that intelligence to guide your defenses.
What makes a threat-led penetration test different from a regular one?
A threat-led test replicates real attacker behavior — not just automated scans. It maps out true Paths to Compromise, giving you actionable insight into how breaches would occur and how to stop them.
How can smaller organizations afford an enterprise-grade posture?
By investing in intelligence-driven defenses like honeypots, credential canaries, and targeted hardening, you can achieve the same level of protection major enterprises have without the enterprise price tag.